Navigating the Digital Maze: Data Integrity in Health Information Systems

Why Bad Health Data Is Costing You Lives and Money—And How to Fix It Now
Data integrity in health information systems is the foundation of modern healthcare, referring to the accuracy, completeness, and reliability of patient information. When it fails, the consequences are severe: medication errors, missed diagnoses, regulatory penalties, and patient deaths.
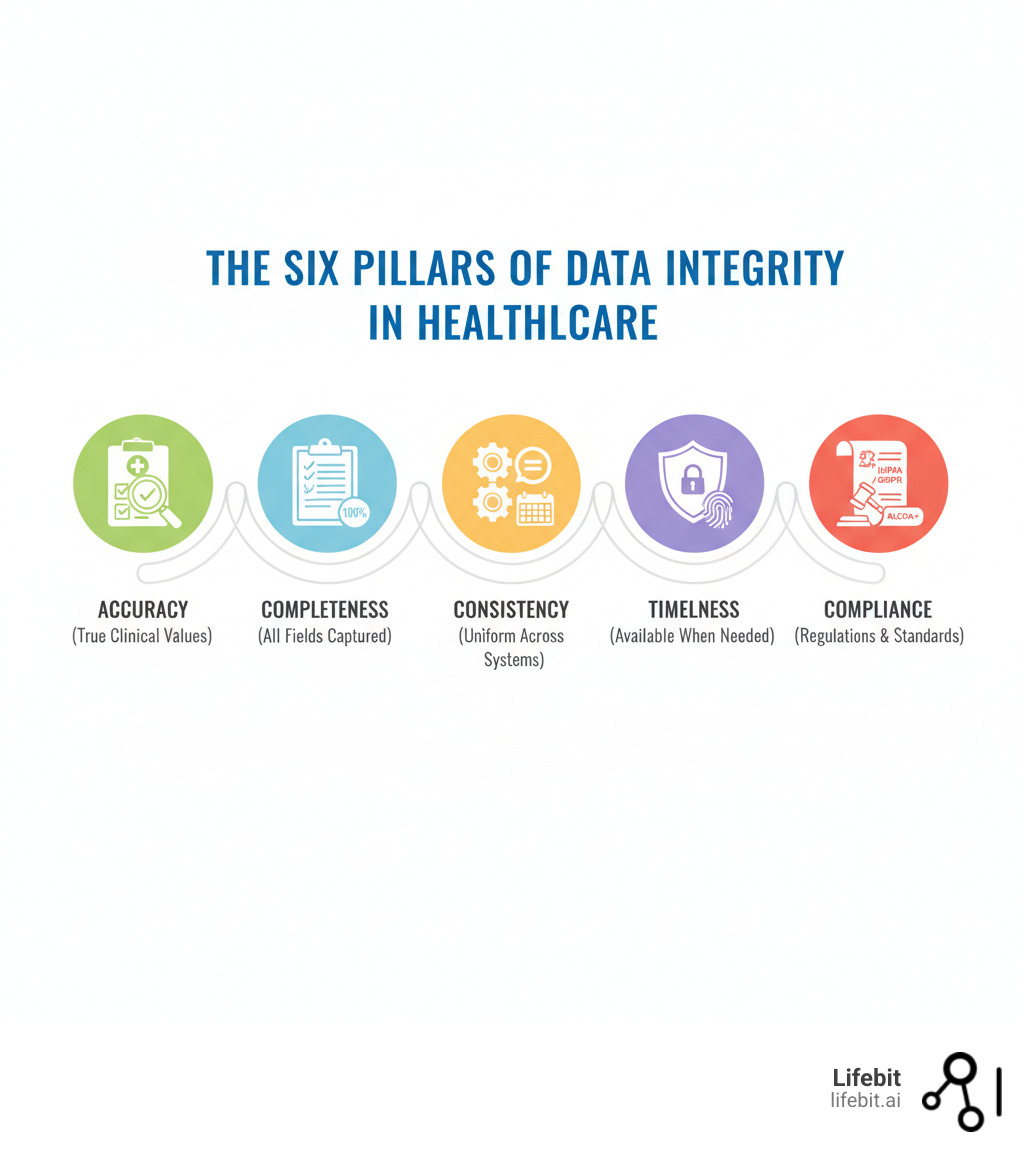
Quick Answer: Essential Guidelines for Data Integrity in Health Information Systems
- Accuracy: Ensure all data reflects true clinical reality without errors
- Completeness: Capture all necessary information without gaps
- Consistency: Maintain uniform data across all systems and time points
- Timeliness: Make data available when needed for clinical decisions
- Security: Protect data from unauthorized access or tampering
- Compliance: Follow ALCOA+ principles (Attributable, Legible, Contemporaneous, Original, Accurate + Complete, Consistent, Enduring, Available)
The stakes are staggering. Healthcare data breaches surged from 6 million affected records in 2010 to 170 million in 2024, with 81% attributed to hacking. Meanwhile, 46% of provider notes contain copied text, introducing dangerous inaccuracies. The cost is immense, with IT incidents accounting for 62% of the largest attacks and records selling for up to $1,000 on the dark web. However, the upside is just as significant. A 2024 NCQA article showed improved data accuracy led to a 25% increase in adult BMI reporting and a 40% improvement in childhood immunization tracking, proving that better data directly improves patient outcomes.
Establishing clear data integrity guidelines is essential for survival. Whether you’re a global pharma company, a regulatory body like the FDA, or a public health ministry, the principles are the same.
I’m Maria Chatzou Dunford, CEO and Co-founder of Lifebit. For over 15 years, I’ve focused on building secure, federated platforms that enable data integrity in health information systems for pharmaceutical and public sector clients globally. My work in computational biology and AI has shown me that data integrity is critical not just for compliance, but for powering the precision medicine revolution.
Let’s break down how to build and maintain data integrity in your health information systems, starting with the hidden dangers that undermine it.
The Hidden Dangers: What’s Undermining Data Integrity in Health Information Systems?
When data integrity in health information systems breaks down, clinicians are forced to make critical decisions with conflicting information, a daily reality that puts patient safety at risk. The culprits behind this chaos are often hiding in plain sight, stemming from systemic fragmentation, human fallibility, and malicious external threats.
Data fragmentation is a primary threat. Patient information is scattered across disconnected systems—hospital EHRs, lab databases, pharmacy records, and specialist software—each with its own codes and version of the truth. This digital Tower of Babel arises from decades of uncoordinated IT adoption, mergers and acquisitions that stitch together incompatible systems, and specialized departments purchasing best-of-breed software without a central integration strategy. A patient’s journey might involve a primary care physician using one EHR, a cardiologist using another, and a diagnostic lab with its own proprietary system. Without robust interoperability standards like FHIR (Fast Healthcare Interoperability Resources) being universally adopted, this data remains siloed. This creates an incomplete picture of patient health, making accurate care coordination nearly impossible and leading to dangerous gaps in knowledge, redundant testing, and delayed diagnoses.
Human and Systemic Errors
In healthcare, a simple typo can be fatal. Manual data entry is a minefield for errors like misplaced decimal points in dosages, transposed digits in lab values, or selecting the wrong patient from a dropdown menu. The problem is compounded by time-saving shortcuts born from immense pressure and poorly designed systems. A study found that 46% of provider notes contained copied text, propagating outdated or inaccurate information throughout a patient’s record.
This copy-paste culture, often called “note bloat,” creates a dangerous illusion of documentation. An initial, incorrect diagnosis or an allergy that has since resolved can be copied forward for years, becoming an unverified “fact” that misleads future care teams. The true timeline of a patient’s condition becomes impossible to reconstruct. Another systemic issue is alert fatigue, where clinicians are bombarded with so many low-priority notifications from the EHR that they begin to automatically dismiss them, potentially ignoring a critical warning about a drug interaction or a data inconsistency.
Lack of interoperability between EHR systems multiplies these issues. When data is manually re-entered between facilities, different coding standards (like ICD-10 for diagnoses and LOINC for lab tests) and formats cause information to be lost or mistranslated. A nuanced diagnosis in one system can become a generic, less-accurate code in another. Furthermore, with 85% of devices in medical organizations running on outdated operating systems, the digital foundation for patient care is crumbling, increasing vulnerability to both data loss and cyberattacks.
Escalating Cybersecurity Risks
While internal errors chip away at data integrity, cybercriminals are taking a sledgehammer to it. A single patient record can sell for up to $1,000 on the dark web, containing a treasure trove of personal and financial information ripe for identity theft and fraud.
The numbers are chilling: healthcare data breaches exploded from 6 million affected records in 2010 to 170 million in 2024. 81% of these breaches were attributed to hacking, with IT incidents accounting for 62% of the largest attacks.
Ransomware attacks, like the WannaCry attack that crippled the UK’s National Health Service, can shut down hospital operations entirely, forcing the cancellation of surgeries, diverting ambulances, and leaving clinicians to rely on paper records, which are often incomplete. Insider threats, whether malicious (a disgruntled employee selling data) or accidental (a well-meaning staff member falling for a phishing email), add another layer of risk. The rise of connected medical devices (the Internet of Things) also expands the attack surface; unsecured insulin pumps, pacemakers, and patient monitors can become gateways into the hospital network.
Terrifyingly, the average time to detect a healthcare data breach is 236 days. That’s over seven months where compromised data can be altered, stolen, and exploited before anyone even knows there’s a problem. Every connected device and data exchange is a potential vulnerability in a landscape where attackers are growing more sophisticated daily.
The Blueprint: Proven Strategies to Guarantee Data Integrity
Ensuring data integrity in health information systems requires an ongoing commitment to a three-pronged approach: robust governance, strong technical safeguards, and an empowered workforce. These proven strategies can help you build a fortress around your health data, creating a culture of trust and reliability.

Establishing Robust Data Governance and Policies
Data governance is the constitution for your health information, defining the principles, policies, and people that manage data as a strategic asset. Without it, you operate in chaos.
- Clear Data Policies: Create living guidelines for the entire data lifecycle, from collection and storage to access, sharing, and eventual retirement. These policies must be clear, enforceable, and regularly updated.
- Defined Roles and Responsibilities: Establish data stewardship programs to assign ownership and accountability. A Data Steward is a subject-matter expert (e.g., a lead pharmacist) responsible for a specific data domain (e.g., medication data), defining its quality rules and resolving issues. A Data Governance Council, comprising leaders from clinical, IT, and administrative departments, provides oversight and strategic direction.
- Data Classification: Not all data is equally sensitive. Apply appropriate levels of protection based on a classification scheme: for example, Public (e.g., hospital location), Internal (e.g., employee schedules), Confidential (e.g., patient demographic information), and Restricted (e.g., genetic test results, mental health records). This ensures that the most stringent security controls are focused where they matter most.
- Regulatory Adherence: Comply with mandates like HIPAA and GDPR, which require protecting health information from unauthorized alteration. The HIPAA Security Rule specifically mandates integrity controls, while GDPR’s principle of ‘accuracy’ requires organizations to take every reasonable step to ensure that inaccurate personal data is rectified or erased without delay. Non-compliance can lead to bankrupting fines and severe reputational damage.
- Proven Frameworks: Use established roadmaps like HITRUST or NIST Cybersecurity Framework to manage risk and ensure compliance. These frameworks provide a structured approach to implementing controls, saving you from guessing at best practices.
Implementing Technical Safeguards and Best Practices
Technology enforces the rules set by governance. These safeguards are the locks, alarms, and safety nets that protect your data from corruption and unauthorized modification.
- Access Controls and Encryption: Implement strict Role-Based Access Control (RBAC) to enforce the principle of least privilege. For example, a nurse can view and update clinical charts for patients on their assigned ward but cannot access financial data. A billing specialist can see insurance information but not sensitive clinical notes. Complement this with strong encryption for data at rest (on servers and databases) and in transit (as it moves across the network) to make it useless if intercepted.
- Regular Security Audits: Conduct frequent, automated system health checkups and vulnerability scans to identify and patch weaknesses before they can be exploited. This includes penetration testing, where ethical hackers attempt to breach your systems to find holes.
- Immutable Audit Trails: Maintain an unalterable, time-stamped record of who accessed or modified data and when. A comprehensive audit log should capture the user ID, date/time, type of action (create, read, update, delete), the specific data element affected, and the patient identifier. This is crucial for investigating errors, detecting malicious activity, and proving compliance.
- Data Validation Rules: Use automated checks at the point of entry to prevent impossible or incorrect values from corrupting your database. Examples include range checks (a patient’s weight cannot be negative), format checks (a date must be in MM/DD/YYYY format), and cross-field validation (a discharge date cannot be earlier than the admission date).
- Data Cleansing: Regularly run processes to identify and correct or merge duplicate records, standardize inconsistent naming conventions (e.g., “St. John’s” vs. “Saint John’s”), and flag outdated information for review.
- Secure Archiving: Use HIPAA-compliant, SOC2-certified solutions for secure data extraction, migration, and long-term storage. Data integrity must be maintained throughout its entire lifecycle, not just when it is actively in use.
Empowering the Workforce
Your staff is the most critical line of defense for maintaining data integrity in health information systems. A well-trained workforce that understands the why behind security protocols is your strongest asset.
- Comprehensive Training: Educate all staff—from clinicians to administrators—on data management protocols, privacy requirements, and documentation best practices. Training should be role-specific and use real-world scenarios, such as how to correctly identify a patient or what to do upon discovering a data error. Explain how shortcuts can lead to patient harm.
- Cybersecurity Awareness: Conduct regular, engaging training on recognizing phishing attempts, creating strong passwords, and practicing safe browsing to prevent network compromises from a single clicked link. Phishing simulations can be highly effective.
- Accurate Documentation Practices: Promote a “collect once, use many times” principle to reduce redundant data entry and streamline workflows, which naturally improves accuracy. Encourage the use of structured data entry fields over free-text notes whenever possible.
- Address EHR Inefficiencies: Improve the usability of EHR systems to combat clinician burnout. Clunky interfaces and inefficient workflows degrade data quality by frustrating users into taking shortcuts or entering incomplete information. Involve frontline clinicians in the selection, design, and continuous improvement of these critical systems.
Investing in your people creates a culture where everyone acts as a guardian of patient data, making them your strongest defense against both errors and attacks.
The Future Is Here: How Next-Gen Technologies Are Securing Health Data Integrity
The digital health revolution is delivering powerful new tools to protect data integrity in health information systems. Technologies like AI and blockchain are moving from theoretical concepts to essential components for managing the complexity and scale of modern healthcare data.

At Lifebit, we see how these technologies are changing data management. The question isn’t whether to adopt them, but how quickly you can implement them to stay competitive and ensure patient safety.
The Role of AI in Safeguarding Data Integrity in Health Information Systems
Artificial Intelligence and Machine Learning act as tireless data guardians, turning reactive damage control into proactive, predictive protection.
AI’s capabilities include automated anomaly detection, where algorithms constantly monitor data streams to instantly flag unusual entries that signal errors or fraud. For instance, an AI could flag a lab result that is physiologically impossible for a human or drastically deviates from a patient’s historical baseline, prompting a manual review before it contaminates the record. Similarly, it can detect abnormal data access patterns, such as a user suddenly downloading thousands of records, indicating a potential insider threat or compromised account.
Through predictive analytics, AI can also analyze historical error patterns to identify which departments, workflows, or user groups are most likely to generate incorrect data, allowing organizations to implement targeted training and process improvements before errors occur.
AI-driven data cleansing automatically identifies and corrects inaccuracies at scale. Natural Language Processing (NLP) is particularly transformative. With 46% of provider notes containing copied text, a vast amount of critical information is locked in unstructured free text. NLP algorithms can parse these notes, extract meaningful information (like diagnoses, symptoms, and medications), standardize the terminology using medical coding systems like SNOMED CT, and flag inconsistencies. This cleaner, structured data then feeds into clinical decision support systems, enabling AI to provide more accurate treatment recommendations and help clinicians make safer, faster decisions.
Blockchain: The Unbreakable Ledger for Health Data
While AI actively guards data, blockchain provides an immutable foundation that makes tampering virtually impossible. Each piece of data or transaction is a “block” that is cryptographically linked to the previous one, creating a distributed and unbreakable chain. Any attempt to alter a historical record would break the cryptographic link, making the change immediately visible to all participants. This results in tamper-proof records ideal for high-stakes information like patient data, clinical trial results, and supply chain management for pharmaceuticals.
This technology enables improved data traceability, as every action is logged with a permanent timestamp and user ID, which is essential for regulatory compliance and auditing. A key application is secure patient consent management. Imagine a patient using a mobile app to grant a specific research study temporary access to their genomic data. This consent is recorded as a transaction on the blockchain. The research platform can then cryptographically verify this consent before allowing access, and access can be automatically revoked when the consent expires. The patient maintains an unalterable, auditable record of who has accessed their data, for what purpose, and when.
Blockchain also facilitates secure data exchange between different entities, helping to overcome the data fragmentation that plagues healthcare. As noted in scientific research on blockchain for healthcare, the technology is increasingly prioritized for managing data integrity in health information systems, particularly in multi-site clinical trials where proving the integrity of data from various sources is paramount for regulatory submission.
At Lifebit, our federated platform combines AI’s intelligence with blockchain’s immutability to create systems that are both smart and trustworthy. These next-gen technologies are no longer optional upgrades; they are the baseline for any organization serious about protecting patient safety in a data-driven world.
Frequently Asked Questions about Data Integrity
Here are answers to the most pressing questions about data integrity in health information systems.
What are the consequences of poor data integrity in healthcare?
Poor data integrity has severe consequences across the board:
- Patient Harm: Inaccurate or incomplete data leads to misdiagnoses, medication errors, and other adverse events that can be fatal.
- Financial Penalties: Regulatory bodies impose heavy fines for non-compliance. HIPAA violations can cost up to $1.5 million annually per violation type, while GDPR penalties can reach up to 4% of global turnover.
- Reputational Damage: Data breaches and quality issues erode patient trust, which can take years to rebuild and can drive patients to other providers.
- Compromised Research: Flawed data makes public health research unreliable, leading to incorrect conclusions and ineffective health policies that affect entire populations.
How do you measure data integrity?
Measuring data integrity requires a multi-faceted approach:
- Key Performance Indicators (KPIs): Track metrics like data accuracy rate, completeness percentage, and timeliness scores.
- Data Quality Audits: Systematically review record samples to identify error patterns and compliance gaps.
- Validation Rule Reports: Monitor how often automated data validation rules are triggered or overridden to spot training or system issues.
- User Feedback: Listen to frontline clinicians and staff who can identify practical, real-world data quality problems.
- Data Profiling Tools: Scan entire databases to get comprehensive statistics on data quality and identify systemic issues.
What is the difference between data integrity and data security?
Though related, data integrity and data security address different challenges.
Data security focuses on confidentiality—protecting data from unauthorized access. It asks: Can the wrong people get to this data? Measures include encryption and access controls.
Data integrity focuses on trustworthiness—ensuring data is accurate, complete, and reliable. It asks: Is this data correct? Measures include data validation rules and audit trails.
You can have perfect security with zero integrity. For example, an incorrect blood type can be stored in a highly encrypted, secure database. The data is secure, but it’s wrong and dangerous.
You need both. Security protects data from external threats, while integrity ensures the data you are protecting is accurate and reliable. At Lifebit, our federated platform is built on both principles, because in healthcare, having information that is both secure and trustworthy is non-negotiable.
Conclusion: Act Now—Build a Federated, Future-Proof Health Data Platform or Get Left Behind
The digital health revolution isn’t coming—it’s here. And it’s moving faster than most organizations realize. The shift towards value-based care, the explosion of multi-omic data, and the growing demand for truly personalized medicine all depend on one critical foundation: data integrity in health information systems. Without this foundation, every advanced technology, every AI algorithm, and every promise of precision medicine becomes unreliable at best and dangerous at worst.
We’ve explored the very real challenges facing healthcare today. Cyberattacks are escalating—remember, 81% of healthcare data breaches are attributed to hacking, with 170 million records compromised in 2024 alone. Human error continues to chip away at data quality, with 46% of provider notes containing potentially inaccurate copied text. And systemic fragmentation means patient data often exists in disconnected silos, making it nearly impossible to assemble a complete, trustworthy picture of health.
But here’s the encouraging news: the solutions aren’t theoretical. They’re proven, actionable, and within reach. Robust data governance establishes the rules and accountability structures that prevent chaos. Advanced technical safeguards—from encryption and access controls to AI-powered anomaly detection and blockchain-based audit trails—create multiple layers of protection. And perhaps most importantly, an empowered, well-trained workforce serves as the first and most critical line of defense in maintaining data quality every single day.
The future of healthcare isn’t just about collecting more data—it’s about having trustworthy data available in real-time for actionable insights. This requires a fundamental shift from isolated systems to federated data ecosystems that can securely connect information across organizations, regions, and countries. These platforms enable real-time access to global biomedical and multi-omic data while maintaining the highest standards of data integrity through built-in harmonization, advanced AI/ML analytics, and federated governance.
Whether you’re a pharmaceutical company conducting global clinical trials, a regulatory body like the FDA needing real-time pharmacovigilance, or a public health ministry tracking disease patterns across populations in the USA, UK, Europe, Canada, Singapore, or Israel, the principle remains the same: data integrity in health information systems is non-negotiable.
The organizations that recognize this urgency and invest now in building secure, federated health data platforms will define the next era of healthcare. They’ll deliver safer care, accelerate breakthrough findies, and truly personalize treatment in ways we’ve only dreamed about. Those who delay risk being left behind as the digital health landscape transforms around them.
The time to act is now. The technology exists. The frameworks are proven. The only question is: will you lead the change, or watch it happen from the sidelines?

