All About Biomedical Data Access

Why Biomedical Data Access Matters More Than Ever
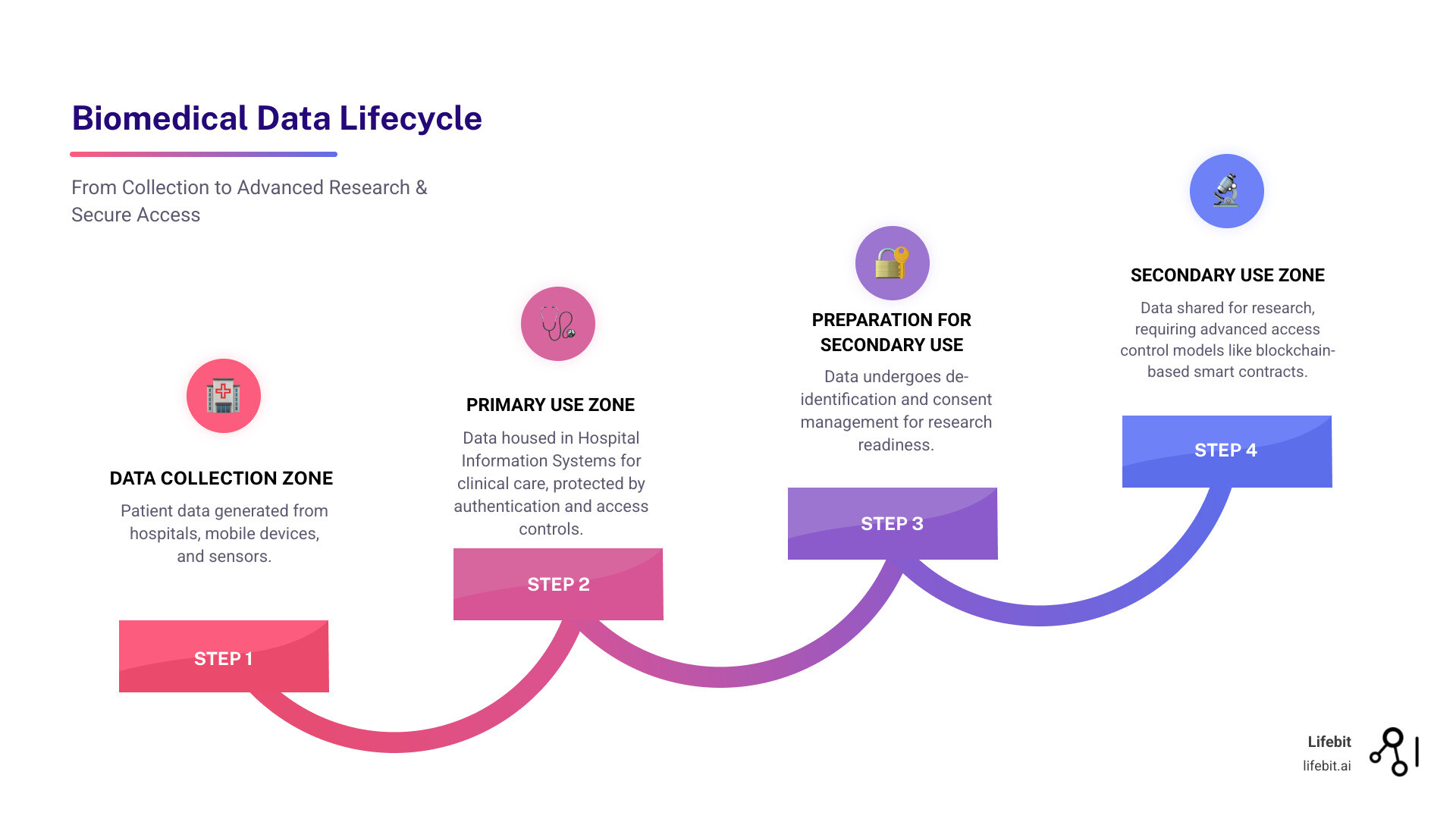
Biomedical data access is the ability for researchers, clinicians, and organizations to find, retrieve, and analyze health information—ranging from electronic health records (EHRs) to genomic sequences—while maintaining privacy, security, and regulatory compliance. Here’s what you need to know:
- Open-access data is freely available without authentication (e.g., aggregate-level datasets, high-level genomic data)
- Controlled-access data requires prior authorization through Data Access Committees (e.g., individual-level data, low-level genomic sequencing)
- Trusted Research Environments (TREs) enable secure, in situ analysis without moving sensitive data
- FAIR principles (Findable, Accessible, Interoperable, Reusable) guide modern data sharing strategies
- Federated platforms allow analysis across distributed datasets while keeping data at its source
The promise of biomedical big data is enormous. Programs like the All of Us Research Program are building some of the largest biomedical data resources ever assembled, storing health data from hundreds of thousands of participants. This data could revolutionize our understanding of disease pathogenesis, accelerate precision medicine, and improve healthcare for everyone.
But there’s a problem.
The very characteristics that make biomedical data valuable—its large volume, velocity, diversity, and sensitivity—also make it incredibly difficult to access and manage securely. Between 15% and 17% of US adults have changed their healthcare-seeking behavior specifically to protect their privacy. Privacy breaches have led to substantial losses for healthcare systems. In February 2017, two staff members of Shanghai CDC illicitly appropriated 200,000 pieces of information on newborn babies. In September 2022, a Kaiser Permanente employee unauthorizedly accessed a patient’s medical record.
Traditional access control methods like Discretionary Access Control (DAC), Mandatory Access Control (MAC), and Role-Based Access Control (RBAC) are static and unable to adapt to the dynamic, real-time characteristics of medical big data scenarios. They’re also susceptible to single points of failure in centralized systems.
As someone who has spent over 15 years working at the intersection of computational biology, genomics, and secure biomedical data access, I’ve seen how these challenges slow down critical research. I’m Maria Chatzou Dunford, CEO and Co-founder of Lifebit, where we’ve built a platform that enables secure, federated biomedical data access across distributed environments without moving sensitive data.
This guide will walk you through everything you need to know about biomedical data access—from understanding the core challenges to implementing next-generation access control models that balance security with usability.
The Core Challenge: Balancing Data Utility with Privacy and Security
The very things that make biomedical data valuable also make it dangerous. Hospital Information Systems generate petabytes of electronic health records, genomic sequences, and medical images. This medical big data could revolutionize healthcare, but it creates a fundamental tension: how do we maximize data utility for research while rigorously protecting patient privacy?
The scale of the problem is staggering. Data comes in every format, and as one research paper noted, “a lack of data interoperability and unified standards has left the promise of precision medicine unfulfilled.” Harmonizing this data is a monumental undertaking. Even with the development of standards like Fast Healthcare Interoperability Resources (FHIR) for exchanging healthcare information electronically and the Observational Medical Outcomes Partnership (OMOP) Common Data Model for standardizing observational data, adoption remains inconsistent. Institutions often use proprietary formats or customized implementations, creating digital siloes that prevent data from being easily combined and analyzed at scale. Privacy fears and security vulnerabilities compound the issue. Public trust is fragile, and traditional security can’t keep up with sophisticated cyberattacks and insider threats. Furthermore, data integrity during hand-offs between research stages is often assumed but rarely validated rigorously.
Other challenges include:
- Dynamic Data: Patient conditions and research protocols evolve, but access control systems are too static to adapt in real-time. A patient’s consent may change, or a clinical trial’s inclusion criteria might be updated, but rigid access rules can’t reflect these shifts without manual intervention, creating delays and compliance risks.
- Training Gaps: Many researchers and clinicians lack formal data management training. This leads to inconsistent data entry, poor documentation, and the creation of unusable “dark data”—information that is collected and stored but is difficult to find, use, or analyze. Without proper metadata and provenance tracking, even accessible data can be worthless.
- Mandate Implementation: Policies like the NIH Data Management and Sharing Policy and the FAIR principles push for open science, but implementation is messy. Organizations struggle with the technical and financial overhead of creating compliant data management plans, establishing repositories, and managing access requests, often without clear guidance or sufficient resources.
Programs like the All of Us Research Program are making strides. Their Data Browser allows exploration of aggregate data, a key step in balancing access and security. Yet, managing these vast, sensitive datasets requires more adaptability and real-time decision-making than traditional models can offer.
Why Traditional Access Control Models Fall Short
Traditional access control models were built for a different era and are inadequate for modern data ecosystems.
- Discretionary Access Control (DAC) puts the resource owner in charge. While this seems flexible, it leads to inconsistent policies and significant risk. For example, a well-meaning principal investigator might grant a junior researcher broad access to a patient dataset, who then unknowingly shares it on an insecure personal device, creating a data breach. The administrative overhead of managing individual permissions across thousands of files and users becomes unmanageable.
- Mandatory Access Control (MAC) assigns sensitivity labels to data (e.g., “Confidential”) and clearance levels to users. It offers high security but is notoriously rigid. Consider a multidisciplinary tumor board where an oncologist, a radiologist, and a geneticist need to collaborate. Under a strict MAC system, they might be blocked from viewing each other’s data if their clearance levels don’t perfectly align with all data labels, stifling the very collaboration needed for comprehensive patient care.
- Role-Based Access Control (RBAC) assigns permissions based on organizational roles (e.g., “doctor,” “nurse,” “researcher”). While simpler to manage than DAC, it remains static and creates a severe over-privileging problem. A nurse assigned to a cardiac ward may get access to all patient records on that floor, including those not under their direct care. This unnecessary access increases the attack surface for both insider threats and external attackers who compromise the nurse’s credentials.
The core issue with all these models is their static nature. They can’t adapt to context, like the time, location, or specific reason for an access request. A doctor accessing a patient’s record at 2 AM from an unfamiliar IP address gets the same permissions as one doing so from their office computer during business hours. This is a major flaw in a world of dynamic threats. In centralized systems, they also create single points of failure. If the central server managing access permissions is compromised, the entire security mechanism collapses. For organizations navigating these challenges, understanding Clinical Data Governance becomes essential.
The Rise of Risk-Adaptive and Dynamic Models
The limitations of traditional models pushed researchers toward Risk-Adaptive Access Control (RAdAC). RAdAC represents a significant leap forward, incorporating risk assessment into every decision. The system evaluates contextual factors—time of day, location, data sensitivity—and adjusts permissions dynamically. An unusual access pattern might trigger extra authentication, aligning much better with the real-world complexity of healthcare.
But here’s the problem: most RAdAC implementations remain centralized. They rely on a central authority for risk assessment, creating a vulnerability that attackers can exploit. If that central system is compromised, the entire access control mechanism could be bypassed or disabled. The industry needed a decentralized, robust, and tamper-proof solution that could maintain RAdAC’s dynamic risk awareness while eliminating single points of failure. That’s where blockchain technology enters the picture.
The Future of Secure Biomedical Data Access: Blockchain and Risk-Based Models
The limitations in traditional and centralized risk-adaptive models are roadblocks preventing us from opening up the full potential of biomedical data. To enable truly secure, scalable biomedical data access, we must rethink our approach.
The solution combines decentralization through blockchain technology with intelligent risk assessment. Together, they create a system that is more secure and adaptable to the complex world of medical research.
The Role of Blockchain and Smart Contracts in Biomedical Data Access
Think of blockchain as a shared, immutable ledger. This decentralized, tamper-proof nature is ideal for managing access to sensitive data. It mitigates single point of failure by distributing control across multiple nodes, ensuring the system remains resilient and available. We explore this concept further in our piece on Decentralized AI Platform.
Every access attempt is recorded on the blockchain as a tamper-proof access log, creating an unalterable audit trail for accountability and forensic analysis. This immutability is achieved through cryptography. Each block of transactions is linked to the previous one using a cryptographic hash. Any attempt to alter a past transaction would change its hash, which would break the chain and be immediately rejected by the network. Smart contracts automate policy enforcement. These self-executing programs live on the blockchain and apply access rules consistently and transparently, reducing human error and administrative overhead.
A key practical consideration is storing EHRs off-chain. Putting entire health records on a public blockchain is impractical due to cost, performance limitations, and privacy concerns. Instead, a hybrid approach is used: the sensitive data itself lives in secure, compliant off-chain storage (like an institutional server or a purpose-built Trusted Research Environment), while the blockchain stores only the metadata, access permissions, and a cryptographic hash (a unique digital fingerprint) of the off-chain data. This hash allows anyone to verify the integrity of the data without ever seeing the data itself. Using generic cloud services or IPFS for the off-chain component may not meet the stringent security and privacy requirements of healthcare data (like HIPAA or GDPR). This is why purpose-built secure environments, which provide granular control and robust security postures, are essential. Our work on Federated Data Governance explores these hybrid models in greater detail.
Introducing the SCR-BAC Model: A Dynamic Approach to Biomedical Data Access
The Smart Contract and Risk-Based Access Control (SCR-BAC) model is the next evolution in secure biomedical data access. It combines blockchain’s decentralization with sophisticated risk quantification to adapt to threats in real-time.
SCR-BAC quantifies risk by examining both current and historical user behavior. It flags unusual requests (e.g., a cardiologist accessing psychiatric records) and maintains a record of past access patterns. A time decay factor gives more weight to recent activity, allowing the system to recognize behavioral changes and prevent a user’s risk score from being permanently tainted by a single past mistake.
Crucially, SCR-BAC differentiates honest and malicious users. Instead of using a simple average risk score, which could be skewed by normal fluctuations, the model calculates dynamic risk thresholds based on the historical profiles of known malicious actors. This statistical approach is far more precise at distinguishing suspicious activity from legitimate, if unusual, access patterns. In simulations, malicious doctors showed risk values 9.5 to 13 times higher than honest doctors, proving the model can effectively distinguish legitimate activity from potential misuse.
Here’s how different access control approaches stack up:
| Feature | Traditional (DAC, MAC, RBAC) | Centralized RAdAC | Decentralized SCR-BAC (Lifebit) |
|---|---|---|---|
| Adaptability | Low (static rules) | Medium (dynamic, but central) | High (dynamic, distributed) |
| Privacy/Security | Moderate | Good (risk-aware) | Excellent (immutable, risk-aware) |
| Single Point of Failure | Yes | Yes | No (blockchain-based) |
| Auditability | Limited | Centralized | Excellent (immutable ledger) |
| Transparency | Low | Centralized | High (smart contract logic) |
| Scalability | Good | Good | High (hybrid off-chain storage) |
| Contextual Awareness | Low | Medium | High (historical & current risk) |
Key Components of the SCR-BAC Model
The SCR-BAC model operates through three interconnected smart contracts on the blockchain:
- The Management Contract is the administrative foundation. It manages user identities, assigns roles (e.g., “doctor,” “researcher”), and defines initial permissions. When a new user is onboarded, this contract registers their digital identity and establishes their baseline access rights within the system, acting as the foundational layer of trust.
- The Access History Contract functions as an immutable, time-stamped log. It permanently records the details of every access event—who, what, when, where, and the purpose of the request—whether it was successful or denied. This tamper-proof audit trail is critical for accountability, forensic analysis after a potential incident, and demonstrating regulatory compliance to auditors.
- The Policy Contract contains the system’s intelligence. It holds the logic for defining access rules, calculating risk scores, and setting the dynamic risk threshold. For each access request, it queries the Access History Contract to retrieve the user’s past behavior, applies the time decay factor to weigh recent activity more heavily, and computes a real-time risk score based on attributes like user role, data sensitivity, time of day, and request frequency.
Determining the risk threshold is a key innovation. The Policy Contract doesn’t use a fixed number. Instead, it dynamically calculates the threshold based on the statistical distribution of historical risk patterns from known malicious users. This makes the system more sensitive to genuine threats while significantly reducing the false positives that plague simpler systems.
By deploying these contracts on a blockchain, the SCR-BAC model inherently mitigates single point of failure vulnerabilities. Access decisions are automatically and transparently enforced by the smart contracts, ensuring consistent and resilient protection for sensitive medical data. This distributed, automated, and intelligent approach is fundamental to securing valuable assets in environments like Trusted Research Environments and Secure Research Environments.
Evaluating and Implementing Next-Generation Access Control
So how do we know these blockchain-based, risk-adaptive models actually work in the real world? After all, we’re dealing with some of the most sensitive data imaginable. The answer lies in rigorous testing and measurable outcomes.
Researchers validate models like SCR-BAC through carefully designed simulations that mirror real-world medical environments. These aren’t just theoretical exercises—they’re practical tests using datasets that reflect the actual scale and complexity of modern healthcare systems.

How SCR-BAC Compares to Existing Models
The experimental methodology for evaluating SCR-BAC involved a substantial simulated environment—think 1,200GB of storage, 1,360 data tables, and over 2.1 million records. Researchers populated this system with 600 simulated doctors, where 90% behaved honestly and 10% exhibited malicious patterns, such as attempting to access records beyond their legitimate scope at a 5% over-access rate.
The results were striking. The risk values for malicious doctors were consistently 9.5 to 13 times higher than those of honest doctors. This wasn’t a subtle difference—it was a clear, statistically significant signal that the model could accurately identify problematic behavior in near real-time.
When it came to actual performance metrics, SCR-BAC outperformed existing schemes across the board. The model achieved 100% precision in identifying the top 10 highest-risk users. That means when SCR-BAC flagged someone as a high-risk threat, it was always correct—no false alarms wasting security teams’ time. The recall rate exceeded 80% when sufficient access information was available, meaning the system caught the vast majority of malicious actors. The F1 scores, which balance precision and recall, consistently demonstrated superior performance compared to earlier models.
But perhaps most impressive was how the system responded to persistent threats. This wasn’t just about detection; it was about automated mitigation. When a malicious doctor made two consecutive inappropriate access attempts, their access was automatically blocked for 700 seconds. Three consecutive attempts? The block duration jumped to 2,200 seconds. This dynamic, escalating response effectively curbs malicious behavior while allowing legitimate users to continue their work unimpeded.
Implications for Research and Clinical Settings
What does this mean for the people actually working with biomedical data access every day? The impact is transformative.
For clinical settings, these next-generation models provide improved security and privacy through immutable audit trails and decentralized enforcement. Every access attempt is recorded permanently, creating a level of accountability that’s simply impossible with traditional systems. This builds the trust that’s desperately needed—remember, up to 17% of adults have changed their healthcare-seeking behavior due to privacy concerns. Restoring that trust is paramount.
For researchers, the primary benefit is improved data usability without sacrificing safeguards. Instead of navigating bureaucratic approval processes that can take weeks or months, legitimate researchers can gain streamlined access to the data they need. The system makes intelligent, context-aware decisions in real-time, removing bottlenecks while maintaining rigorous security standards.
From Months to Minutes: A Researcher’s Journey Transformed
Consider the typical workflow for a researcher, Dr. Evans, who wants to study the genomic markers of a rare form of cancer.
The Old Way: Dr. Evans identifies three hospitals with relevant patient cohorts. She spends the next six months navigating three separate, paper-based approval processes. She fills out lengthy forms, gets institutional sign-offs, and waits for each hospital’s Data Access Committee to meet and review her request. After finally receiving approval, the hospitals send her three separate, de-identified datasets. The data arrives in different formats with inconsistent coding, forcing her team to spend another three months cleaning and harmonizing the data before a single analysis can be run. The entire process takes nearly a year.
The New Way with Federated, Risk-Based Access: Dr. Evans uses a federated data platform powered by a model like SCR-BAC. She submits a single digital research proposal through a unified portal. The platform’s smart contracts automatically verify her credentials, role, and the project’s ethical approval against on-chain records. The system then grants her permission to run her analysis inside each hospital’s secure environment, without the raw data ever moving or being copied. She pushes her analytical workflow to the data, and the aggregated, non-identifiable results are returned to her in hours. She has accomplished in one afternoon what used to take almost a year, all while providing a higher level of security and a complete audit trail.
This acceleration in secure biomedical data access has profound implications for clinical research. When researchers can access real-world data and genomic information quickly and securely, discoveries happen faster. Precision medicine initiatives move forward. Drug development accelerates. Our work on Federated Data Analysis demonstrates how secure, distributed access enables collaboration that was previously impossible.
These models also directly support growing mandates like the NIH Data Management and Sharing Policy and FAIR data principles. Rather than treating compliance as a burden, blockchain-based access control makes it a natural byproduct of the system’s design. The immutable logs provide a perfect, auditable record for HIPAA compliance, proving who accessed what data and when. For regulations like GDPR, which include the “right to be forgotten,” the hybrid model offers a solution: the off-chain data can be cryptographically erased, and the on-chain access key can be revoked, rendering the data inaccessible while preserving the integrity of the audit log. For practical guidance on navigating these requirements, A practical guide to data management and sharing offers valuable insights.
Perhaps most importantly, these systems enable genuine collaboration. When institutions can share sensitive datasets with confidence, knowing every access is tracked and appropriate, the boundaries between organizations begin to dissolve. Researchers can work together across continents, pooling their data and expertise without compromising patient privacy. Our exploration of Trusted Research Environments for Data Commercialization shows how this secure collaboration opens up new opportunities for innovation.
The efficiency gains are real and measurable. At Lifebit, we’ve seen how our federated platform enables organizations to analyze distributed datasets without the time, cost, and risk of moving sensitive data. This isn’t just about better security—it’s about fundamentally reimagining how we work with medical information to improve patient outcomes and advance human health.
Conclusion
The challenge in biomedical research is urgent. We have more health data than ever—genomic sequences, electronic health records, real-world evidence—holding answers to our biggest questions about disease. But secure access remains the primary bottleneck.
Traditional access control models force an impossible choice: lock down data so tightly that researchers can’t use it, or open it up and risk privacy breaches that erode patient trust.
The good news? We no longer have to choose.
Decentralized, risk-aware models like SCR-BAC offer a new path. By combining blockchain’s immutability with real-time risk assessment, we can build systems that adapt to user behavior and provide tamper-proof audit trails. Simulations show these models achieving 100% precision in identifying high-risk users while maintaining over 80% recall and effectively blocking repeated malicious attempts.
In practice, this means researchers get the data they need, when they need it, without compromising privacy. Compliance with mandates like the NIH Data Management and Sharing Policy becomes streamlined. We can finally deliver on the promise of precision medicine because biomedical data access is no longer the bottleneck.
The future of secure collaboration in biomedical research is decentralized, transparent, and intelligent.
At Lifebit, we’ve built our federated platform on these principles. We enable secure, real-time biomedical data access across distributed environments, allowing researchers to analyze global, multi-omic data while keeping sensitive information in place. Our Trusted Research Environment (TRE), Trusted Data Lakehouse (TDL), and R.E.A.L. (Real-time Evidence & Analytics Layer) deliver the security, compliance, and analytical power that modern biomedical research demands.
The question isn’t whether to adopt next-generation access control—it’s how quickly you can implement it. Every day we wait is another day of potential findies locked away.
Learn how Lifebit enables secure, real-time biomedical data access

