How to Master Secure Cloud Data Governance Without Losing Your Mind

Why Secure Cloud Data Governance Is No Longer Optional
Secure cloud data governance is the set of policies, processes, and technical controls that protect your data — and prove you’re handling it responsibly — across public, private, and hybrid cloud environments. In the modern enterprise, data is no longer a static asset sitting in a basement server; it is a fluid, high-velocity resource that powers everything from customer experience to life-saving drug discovery. However, this fluidity introduces significant risk. Without a structured approach to governance, the cloud becomes a “black box” where sensitive information can be leaked, mismanaged, or non-compliant with international law.
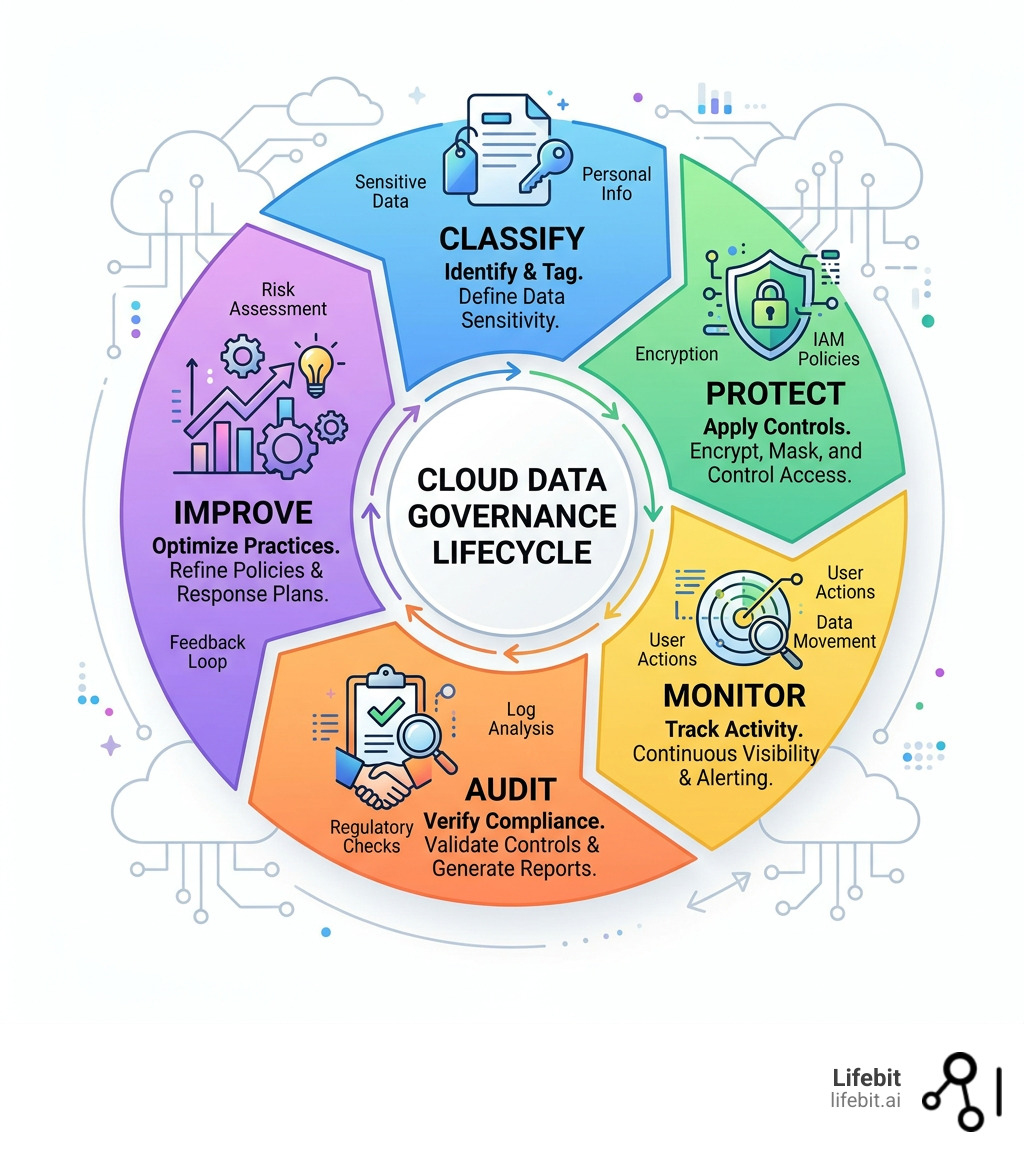
To understand the scope of this challenge, we must look at the core pillars of a governance strategy. It is not merely about security; it is about the intersection of security, compliance, and utility. Here’s what it covers at a glance:
| Core Area | What It Means |
|---|---|
| Data visibility | Know where your data lives, who can access it, and how it moves across multi-cloud environments. |
| Access control | Restrict data access by role, attribute, or purpose using the principle of least privilege. |
| Regulatory compliance | Meet GDPR, HIPAA, CCPA, and other mandates automatically through policy-as-code. |
| Data quality | Ensure data is accurate, complete, and trustworthy for AI and business decisions. |
| Audit readiness | Maintain lineage and logs to prove compliance at any time without manual intervention. |
| Security enforcement | Encrypt, mask, and monitor sensitive data continuously to prevent unauthorized exposure. |
The stakes have never been higher. Global public cloud spending hit $675 billion in 2024 — a 20% jump from the year before. This massive migration has outpaced the development of internal security protocols. More data in the cloud means more exposure. In that same year, 61% of companies experienced at least one cloud security issue, and for 1 in 5 of those, it resulted in an actual data breach. These aren’t just statistics; they represent lost intellectual property, compromised patient records, and massive financial hits.
Regulators are watching too. In October 2024, LinkedIn was fined €310 million by Ireland’s Data Protection Commission for processing personal data without a lawful basis — a stark reminder that poor governance isn’t just a technical problem. It’s a business risk that can lead to multi-million dollar penalties and permanent brand damage.
And yet, according to Gartner, 80% of organizations trying to scale digital operations will fail by 2025 simply because they haven’t modernized how they govern data. They are trying to apply 20th-century manual processes to 21st-century automated infrastructure. The good news? With the right framework, governance doesn’t have to be a bottleneck. It can be the engine that makes your data more usable, not less, by providing a foundation of trust.
I’m Dr. Maria Chatzou Dunford, CEO and Co-founder of Lifebit, where I’ve spent over 15 years building secure, federated data platforms for some of the world’s most compliance-sensitive environments — from national genomics programmes to pharmaceutical research — making secure cloud data governance central to everything we do. In this guide, I’ll walk you through the frameworks, tools, and practices that actually work at scale.
Common secure cloud data governance vocab:
Why Secure Cloud Data Governance is the Only Way to Survive 2025
In the old days of on-premise servers, “governance” meant locking a room and keeping a spreadsheet of who had the key. Today, our data lives in a sprawling mix of public, private, and hybrid cloud environments. This dynamic infrastructure scales in seconds, but it also creates “shadow data”—sensitive information that lives outside the view of IT and security teams. Shadow data often occurs when developers spin up temporary databases for testing or when business units use unsanctioned SaaS tools, leaving a trail of unprotected PII (Personally Identifiable Information) across the web.
Without a robust strategy for secure cloud data governance, you aren’t just risking a minor leak; you’re inviting a catastrophic breach. In 2024, high-profile incidents involving cloud accounts at major companies like Ticketmaster and AT&T showed that even massive organizations can fall victim to unauthorized access when monitoring isn’t centralized and continuous. These breaches often stem from simple misconfigurations or stolen credentials that go undetected because there is no unified governance layer to flag the anomaly.
The High Cost of Compliance Failure
The era of “move fast and break things” is over for data. Data privacy regulations have become global and aggressive. Whether you are dealing with GDPR regulatory requirements in Europe, CCPA privacy standards in California, or HIPAA health data protection in the US, the rules are strict and the enforcement is real.
Failing to implement these isn’t just about the fines—though the LinkedIn €310 million GDPR fine proves they can be devastating. It’s about brand reputation and the “social license” to operate. According to the IBM Cost of a Data Breach Report 2024, the average cost of a breach has climbed to nearly $4.9 million, with highly regulated industries like healthcare and finance seeing costs nearly double that average.
Once a research organization or biopharma company loses the trust of its participants or patients, that data ecosystem becomes impossible to rebuild. Patients will not share their genomic data if they fear it will be leaked to insurers or hackers. Modern governance ensures that legal, regulatory, and corporate rules are baked into the cloud architecture from day one, transforming security from a reactive cost center into a proactive business enabler.
The 4 Pillars of a Modern Cloud Governance Framework
Implementing secure cloud data governance requires moving beyond static PDF documents that sit on a shelf. We need a living, breathing framework that scales at the speed of the cloud. The Cloud Data Management Capabilities (CDMC) framework, developed by the EDM Council with input from over 300 professionals, provides a gold standard for this, focusing on automated controls and measurable outcomes.

To build a framework that doesn’t crumble under the weight of petabyte-scale data, we focus on these four pillars:
- Automated Discovery and Classification: You cannot govern what you cannot see. Organizations must use AI-driven tools to scan for cloud-native, shadow, and dark data. This includes identifying sensitive elements across structured databases and unstructured formats like chat logs, clinical notes, or PDF reports. Classification should be dynamic; as data changes, its sensitivity label should update automatically.
- Unified Access Control: We use a combination of Role-Based Access Control (RBAC) and Attribute-Based Access Control (ABAC) to ensure the principle of least privilege. While RBAC assigns permissions based on a job title, ABAC allows for more granular rules—for example, “allow a researcher to see this data only if they are in the UK, using a secure VPN, and the data is for Project X.” In a Data Lakehouse Governance model, this means permissions are managed at the account level down to the specific row or column.
- Data Sovereignty and Lineage: In a global research environment, knowing where data resides is critical for jurisdictional compliance. Laws like Schrems II have made cross-border data transfers a legal minefield. Data lineage provides a transparent map of how data moves from its origin to its final destination, which is essential for audit trails and ensuring that data never leaves its required geographic boundary.
- Security by Design: This includes encryption (using customer-managed keys so the cloud provider cannot see the data), dynamic data masking, and the implementation of Cloud Data Management Capabilities (CDMC) Framework controls to ensure ethical AI use and data protection. Security should not be an afterthought added at the end of a project; it must be the foundation upon which the project is built.
Security Features for Secure Cloud Data Governance
A truly secure data environment doesn’t rely on a single firewall. It uses a “defense in depth” strategy. Key features include:
- Dynamic Data Masking: This allows for real-time obfuscation of sensitive data. A service agent might see only the last four digits of an ID, while a researcher with higher clearance sees the full value, all without changing the underlying data.
- Zero-Trust Models: The core philosophy is “never trust, always verify.” Every access request is authenticated and authorized based on context (user, device, location, time), not just because the user is on the internal network.
- Data Provenance: This goes beyond lineage to track the “who, what, and when” of every data transformation. This is vital for AI/ML models to ensure that the training data hasn’t been tampered with or biased.
Automating Compliance: From Policy-as-Code to Continuous Monitoring
Manual audits are the enemy of scale. If your compliance team is still manually checking permissions once a quarter or using spreadsheets to track data access, you are already out of date and likely out of compliance. The future of secure cloud data governance is automation.
By using “Policy-as-Code,” we can embed governance rules directly into infrastructure templates (like Terraform or CloudFormation). This prevents “policy drift,” where cloud settings slowly become less secure over time due to manual changes. When combined with a federated data governance approach, organizations can maintain control over data that stays in its original location. This is particularly vital for international research collaboration where data cannot legally be moved across borders but needs to be analyzed collectively.
How to Automate Your Compliance in 5 Steps:
- Identify Mandates: Document specific requirements for GDPR, HIPAA, or CCPA based on your geography and industry. Don’t just list the laws; translate them into technical requirements (e.g., “All PII must be encrypted with AES-256”).
- Apply Policy-as-Code: Use templates to enforce consistent security settings at deployment. If a developer tries to spin up an unencrypted S3 bucket, the system should automatically block the action.
- Automate Tagging: Use AI-enabled data governance tools to automatically label data by sensitivity and content type the moment it is created or uploaded.
- Continuous Auditing: Set up real-time alerts for misconfigurations or unauthorized access attempts. Instead of a quarterly report, you get a real-time dashboard of your compliance posture.
- Centralized Reporting: Aggregate findings into a shared dashboard for instant audit readiness. When a regulator asks for proof of compliance, you should be able to generate a report in minutes, not weeks.
Best Practices for Secure Cloud Data Governance
We recommend an “Agile Governance” approach. Instead of trying to lock everything down in a massive, multi-year project that frustrates users, start with small, iterative improvements. Focus on your highest-risk datasets first—typically PII or proprietary research data.
Another critical practice is ROT data minimization. Redundant, Obsolete, and Trivial (ROT) data clutters your environment, increases storage costs, and expands your attack surface. Every byte of data you don’t need is a byte you don’t have to secure. Using AI to identify and purge these files reduces risk and improves the accuracy of your AI models. Whether you choose centralized vs decentralized data governance, the goal remains the same: high-quality, trustworthy data that is available to those who need it and invisible to those who don’t.
Overcoming Data Sprawl and Team Silos in Multi-Cloud Environments
Multi-cloud environments are the new reality for 90% of enterprises, but they bring massive complexity. Different clouds (AWS, Azure, Google Cloud) have different security tools, terminology, and logging formats. This leads to silos where IT, Security, and Business teams don’t speak the same language, and security gaps fall through the cracks between providers.
To overcome this, organizations need a data governance platform that acts as a unified “pane of glass.” This allows for scalable data sharing—like using open protocols to share live data without actually copying it—while maintaining strict security boundaries. This is often referred to as a “Data Mesh” or “Data Fabric” approach, where governance is decentralized to the teams who know the data best, but overseen by a central policy engine.
Alignment across teams is achieved when governance is seen not as a “no” department, but as a facilitator of secure, real-time insights. When a researcher can access a dataset in minutes because the governance is automated, they become the biggest advocates for the system.
Measuring the Success of Secure Cloud Data Governance
How do you know if your governance is actually working? You cannot manage what you do not measure. We look at these Key Performance Indicators (KPIs):
- Audit Readiness: How long does it take to generate a full compliance report for a specific dataset? (Goal: Minutes, not weeks).
- Risk Reduction: Are we seeing a decrease in the number of misconfigured cloud buckets or “shadow” data assets discovered during scans?
- Data Accuracy: Is the data being used for AI/ML consistently high-quality? What percentage of data is flagged as “ROT” and successfully purged?
- Access Latency: Are researchers getting the access they need within an acceptable timeframe, or are they resorting to unsecure workarounds like sharing passwords?
- Policy Coverage: What percentage of your total cloud estate is covered by automated Policy-as-Code templates?
Our Lifebit approach to data governance & security emphasizes that success is found when security and usability are perfectly balanced. If security is too tight, people bypass it. If it’s too loose, you’re at risk. The “sweet spot” is automated, transparent governance.
Frequently Asked Questions about Secure Cloud Data Governance
How can organizations automate cloud compliance and audits?
Automation is achieved through Policy-as-Code, which enforces rules at the infrastructure level, and continuous monitoring tools that flag violations in real-time. Automated tagging ensures that every new piece of data is classified the moment it is created. This creates a secure data environment (SDE) where compliance is “always on” rather than a point-in-time event. By integrating these tools into the CI/CD pipeline, security becomes a standard part of the development lifecycle.
What role do data catalogs play in cloud governance?
Data catalogs are the “map” of your data estate. They handle metadata management, allowing teams to discover what data exists across different clouds without needing to see the raw data itself. Crucially, they track data lineage, showing the journey of data from its source to its current state, which is a requirement for clinical data governance. A good catalog also includes social features, like data ratings and usage notes, which help researchers understand the quality and context of the data they are using.
How does cloud data governance support AI and ML workloads?
AI is only as good as the data it’s fed. Governance ensures that AI models are built on “trusted data” that is accurate, ethically sourced, and free from unauthorized PII. By maintaining strict lineage and provenance, organizations can prove their AI outcomes are unbiased and compliant with emerging ethical standards like the EU AI Act. For a deeper dive, see our AI-enabled data governance ultimate guide.
What is the difference between Data Residency and Data Sovereignty?
Data residency refers to the physical location where data is stored. Data sovereignty goes a step further, stating that the data is subject to the laws of the country in which it is located. Secure cloud data governance must account for both, ensuring that data stored in Germany, for example, is handled according to German and EU law, even if the cloud provider is a US-based company.
Why is Data Minimization important for cloud security?
Data minimization is the principle of only collecting and keeping the data you absolutely need. In the cloud, every extra gigabyte of data is a potential liability. By implementing ROT (Redundant, Obsolete, Trivial) data deletion policies, you reduce your attack surface and lower your storage costs simultaneously.
Conclusion
Mastering secure cloud data governance is no longer a luxury for the few; it is a survival requirement for any organization operating in the digital age. As we move toward 2025, the complexity of multi-cloud environments and the increasing pressure from global regulators will only intensify. However, by shifting from manual, reactive processes to automated, proactive frameworks like CDMC and Policy-as-Code, you can turn governance from a burden into a competitive advantage.
At Lifebit, we specialize in making this complex process seamless. Our Trusted Research Environment (TRE) and federated AI platform are designed specifically for the world’s most sensitive biomedical data, ensuring that security never comes at the cost of scientific progress. We believe that the most sensitive data in the world should also be the most useful, provided it is governed with precision and integrity. Whether you are managing multi-omic data across five continents or building a local clinical data lakehouse, we provide the tools to keep your data secure, compliant, and ready for discovery.
Ready to secure your data estate and unlock the full potential of your cloud investments? Visit the Lifebit Trust Center to learn more about our commitment to world-class security and governance and how we can help you build a future-proof data strategy.

