The Ultimate Guide to HIPAA Compliant EMR Solutions

Stop HIPAA Nightmares Before They Start: Why Compliant EMRs Are Now Mission-Critical
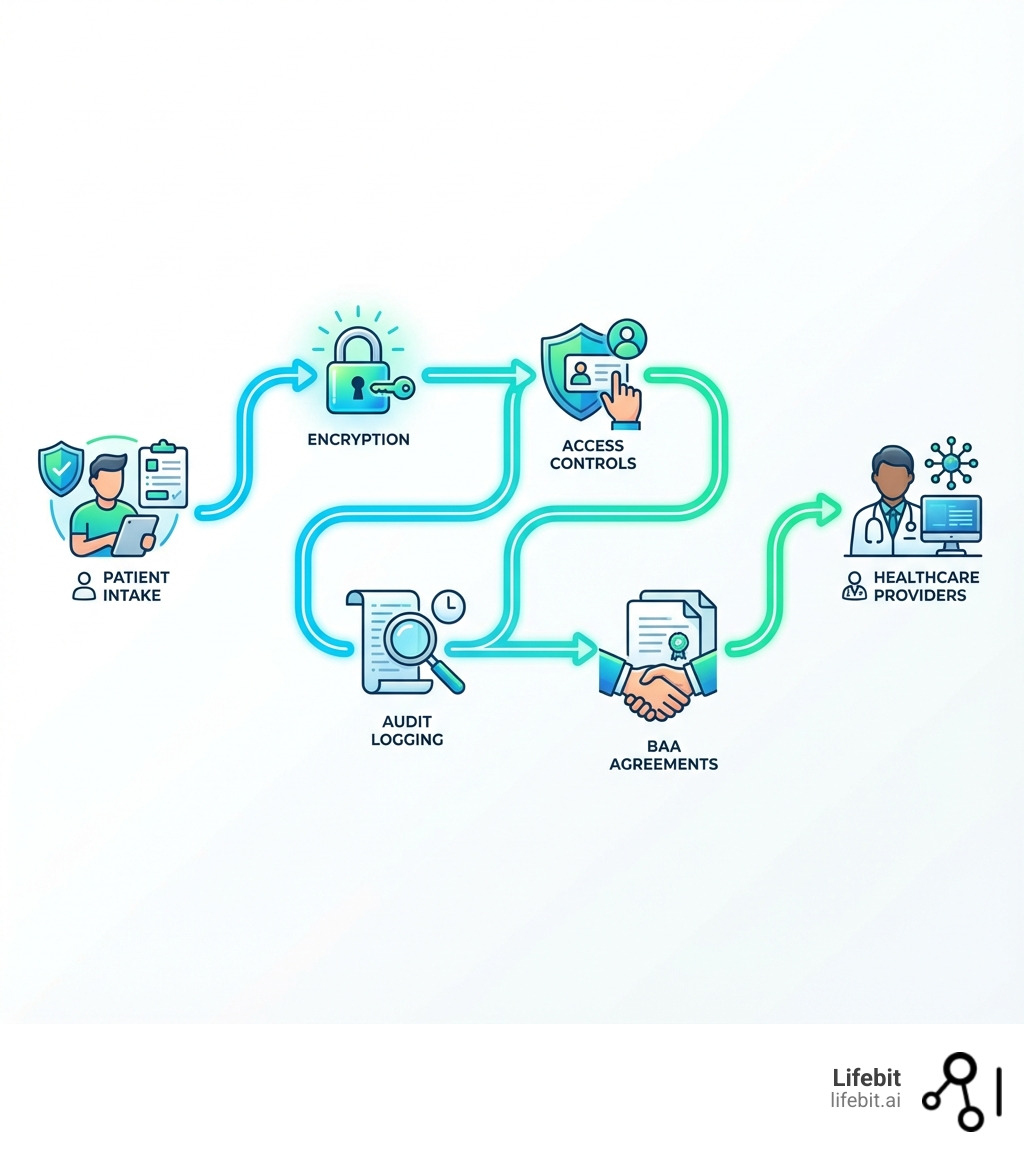
A HIPAA compliant EMR is an Electronic Medical Records system that is specifically engineered to meet all requirements of the Health Insurance Portability and Accountability Act. It protects electronic Protected Health Information (ePHI) through a combination of technical, administrative, and physical safeguards that work together as a single, coherent security framework.
Key requirements for HIPAA compliant EMR systems include:
- Access Controls: Unique user IDs and role-based permissions for every workforce member
- Encryption: Data encrypted both at rest and during transmission
- Audit Trails: Automatic logging of all access and modifications to patient records
- Business Associate Agreements (BAAs): Signed contracts with EMR vendors guaranteeing HIPAA compliance
- Authentication: Multi-factor authentication and automatic session timeouts
- Data Integrity: Controls preventing unauthorized changes or deletion of ePHI
With over 70% of U.S. patient records now digital, storing this sensitive health information carries significant legal obligations and security risks.
U.S. healthcare providers must maintain HIPAA compliance for all electronic health records. Non-compliance leads to severe financial penalties, erodes patient trust, and risks data breaches affecting thousands of patients.
Healthcare organizations are major targets for cyberattacks because they hold large volumes of valuable personal data. Without proper safeguards, an EMR system can quickly become a liability rather than an asset.
Yet many healthcare providers struggle with questions like: Is my EMR vendor truly compliant? What happens when I integrate AI tools or connect with other healthcare systems? How do I prepare for upcoming regulatory changes?
This guide explains what makes an EMR system HIPAA compliant, how to verify vendors, how to identify non-negotiable features, and how to steer challenges like AI integration and interoperability while protecting patient trust.
I’m Maria Chatzou Dunford, CEO and Co-founder of Lifebit, where we help healthcare organizations securely analyze genomic and biomedical data across federated environments while maintaining strict HIPAA compliant EMR standards. Over the past 15 years in computational biology and health-tech, I have seen how the right data infrastructure transforms patient outcomes without compromising security.
What is a HIPAA Compliant EMR and Why is it Non-Negotiable?
At its core, a HIPAA compliant EMR is a digital patient chart designed to meet the strict requirements of the Health Insurance Portability and Accountability Act (HIPAA), a 1996 U.S. law. For any organization handling U.S. patient data, HIPAA compliance is a legal imperative, not just a best practice. Our goal is to ensure that the electronic Protected Health Information (ePHI) within these systems is kept confidential, secure, and available only to authorized individuals.
The HHS’ Office of Information Security defines an EMR as a digital record of a patient’s medical history from a single practice. It primarily allows for the electronic entry, storage, and maintenance of health information. An Electronic Health Record (EHR), on the other hand, is a broader concept, encompassing records from multiple providers and offering a more comprehensive, interoperable view of a patient’s health journey. While EMRs are digital versions of paper charts within a clinic, EHRs are designed to be shared across different healthcare settings. Both, however, must adhere to HIPAA’s strict rules when handling ePHI.
The necessity of a HIPAA compliant EMR goes beyond simply avoiding penalties. It forms the bedrock of patient trust and operational integrity. Healthcare organizations are prime targets for cyberattacks due to the immense volume of sensitive personal data they hold. A single data breach can lead to devastating financial consequences, reputational damage, and a complete erosion of patient confidence. Implementing robust HIPAA compliant EMR solutions safeguards patient privacy, reduces legal risks, and improves the security of healthcare operations.
| Feature | Electronic Medical Record (EMR) | Electronic Health Record (EHR) |
|---|---|---|
| Scope | Digital version of paper charts from a single practice. | Comprehensive digital record from multiple providers and healthcare settings. |
| Focus | Clinical data for diagnosis and treatment within one organization. | Patient-centric, total health over time, designed for sharing. |
| Sharing | Limited sharing, primarily within the practice. | Designed for interoperability and seamless sharing across organizations. |
| Data Type | Medical history, diagnoses, medications, immunizations, allergies. | All EMR data plus demographics, progress notes, problems, lab results, etc. |
| Benefits | Streamlined workflows, internal efficiency. | Improved care coordination, improved patient outcomes, public health reporting. |
| Compliance | Must be HIPAA compliant EMR. | Must be HIPAA compliant, with added focus on secure data exchange. |
The Three Pillars: HIPAA Safeguards Your EMR Must Have
Imagine a fortress guarding invaluable treasures – that’s what a HIPAA compliant EMR system should be for patient data. Our defense strategy relies on three critical pillars of protection outlined by the HIPAA Security Rule: Administrative, Physical, and Technical Safeguards. These aren’t just suggestions; they are mandates that every healthcare entity handling electronic Protected Health Information (ePHI) must implement and document.

Administrative Safeguards
These safeguards are the policies, procedures, and actions that guide how we manage security at an organizational level. They are the human-centric backbone ensuring our team understands their responsibilities and how to protect ePHI.
- Security Management Process: This is the cornerstone of administrative safeguards. It requires conducting a thorough and ongoing risk analysis to identify potential threats and vulnerabilities to ePHI and implementing security measures to mitigate those risks. A proper risk analysis involves identifying all systems containing ePHI, assessing threats (e.g., malware, insider threats), evaluating existing security controls, and determining the likelihood and impact of a breach. This is not a one-time checklist; it’s an iterative process that must be documented and revisited regularly.
- Workforce Training and Security Awareness: Comprehensive and continuous HIPAA training for all staff is paramount. It should cover the organization’s specific security policies, permitted uses of PHI, and how to recognize and report threats like phishing emails, social engineering attempts, and malware. Your team is the first line of defense, and effective training transforms them from a potential vulnerability into a security asset.
- Sanction Policies: To ensure accountability, we must have clear, documented sanction policies for any workforce member who violates security policies or HIPAA rules. These sanctions, which should be applied consistently, help deter non-compliance and foster a culture where security is taken seriously.
- Business Associate Agreements (BAAs): A robust Business Associate Agreement (BAA) is non-negotiable when engaging any third-party vendor that will create, receive, maintain, or transmit ePHI on your behalf. This legally binding contract ensures the partner is held to the same HIPAA standards you are. Sharing ePHI with a vendor without a BAA in place is a direct HIPAA violation.
- Information Access Management: This involves establishing and enforcing policies for authorizing access to ePHI. We ensure that access is granted based on the “minimum necessary” principle—meaning individuals only access the specific information required to perform their job functions. This requires defining user roles and permissions carefully. The policy must also include procedures for promptly revoking access when an employee’s role changes or upon termination.
Physical Safeguards
These safeguards protect our physical environment, hardware, and electronic media from unauthorized access, tampering, or theft. They are the locks, alarms, and procedures that secure our physical premises and devices.
- Facility Access Controls: We must control physical access to facilities where ePHI is stored (e.g., offices, server rooms). This includes using locks, security cameras, visitor logs, and escorting visitors in secure areas. Only authorized personnel should have unescorted access to sensitive locations.
- Workstation Security: All workstations used to access ePHI must be physically secured. This means positioning screens to prevent unauthorized viewing by others (e.g., in a waiting room), using automatic logoffs after a period of inactivity, and enforcing strict rules against sharing login credentials. For portable devices, this includes policies for their use outside the facility.
- Device and Media Controls: This covers the entire lifecycle of hardware and electronic media containing ePHI, from receipt and movement to final disposal. We must implement inventory tracking for all devices (laptops, hard drives, USB drives), create secure data backup and storage plans, and establish formal policies for data disposal. Proper disposal methods like degaussing, pulverizing, or shredding are essential to ensure data cannot be recovered from retired media.
Technical Safeguards
These are the technological controls built into our HIPAA compliant EMR systems and IT infrastructure to protect ePHI from unauthorized access and breaches.
- Access Controls: EMR systems must use unique user identification for each user—sharing logins is a serious violation. Role-based access controls must be implemented to enforce the ‘minimum necessary’ principle at a technical level. The system should also have an emergency access procedure to allow necessary access during a crisis, which must still be documented and audited.
- Audit Controls: All actions within the EMR must be trackable. Audit controls are essential to prevent, detect, contain, and correct security violations. The system must automatically generate immutable audit logs that record events such as user logins, files accessed, data created or modified, and information exported. These logs allow for proactive monitoring and are critical for forensic investigation after a security incident.
- Integrity Controls: To prevent unauthorized alteration or destruction of ePHI, our EMR systems must employ integrity controls. This includes features like requiring electronic signatures for any changes to patient charts (linked to unique usernames) and using checksum verification, which creates a digital fingerprint of data to alert us if it has been tampered with.
- Data Encryption: Encryption acts as a critical safeguard. Data must be encrypted both when it’s “at rest” (stored on servers, laptops, or backup media) and “in transit” (sent across networks). Strong, NIST-approved encryption methods, such as AES-256, are the standard. Importantly, HIPAA provides a “safe harbor” for breached data that is properly encrypted; if encrypted ePHI is lost or stolen, it is not considered a reportable breach, saving organizations from costly notifications and penalties.
- Transmission Security: This safeguard focuses on protecting ePHI when it’s sent electronically over any open network. Our HIPAA compliant EMR systems must use technical security measures to ensure that data remains secure during transmission. This involves using network encryption protocols like TLS (Transport Layer Security) to protect data from interception and integrity controls to prevent it from being altered en route.
Choosing and Verifying a HIPAA Compliant EMR Solution
Selecting a HIPAA compliant EMR is one of the most critical technology decisions a healthcare organization will make. It requires thorough due diligence that goes far beyond a vendor’s marketing claims. Your responsibility as a Covered Entity is to verify that the solution and the vendor meet all necessary compliance and security requirements.

Essential Features of a HIPAA Compliant EMR
When evaluating potential EMR solutions, we look for a suite of features specifically designed with HIPAA compliance and modern healthcare workflows in mind:
- Secure Patient Portal: A portal is vital for patient engagement, allowing them to access their health information, view lab results, and communicate securely with providers. The portal must be fully encrypted, require strong authentication, and log all access to protect ePHI.
- Granular Role-Based Access Controls (RBAC): This feature is paramount. The system must allow administrators to create detailed user roles with specific permissions, ensuring that team members have access only to the ePHI absolutely necessary for their job functions, adhering strictly to the “minimum necessary” principle.
- Comprehensive and Immutable Audit Trails: The EMR must automatically log every action involving ePHI—every access, modification, export, and deletion. These detailed audit trails must be tamper-proof and easily searchable, as they are indispensable for security monitoring, incident response, and proving compliance.
- End-to-End Encrypted Communication: All communications involving ePHI, whether through internal messaging, patient portal messages, or data exchange with other systems, must occur over encrypted channels to prevent unauthorized interception.
- Secure Telehealth Integration: With the rise of remote care, seamless and secure telehealth capabilities are essential. The EMR should integrate with or offer a telehealth solution that is fully HIPAA compliant, including a signed BAA and encrypted video/audio streams.
- Compliant E-prescribing: Secure electronic prescribing improves efficiency and patient safety. The system must ensure the secure transmission of prescription information to pharmacies, adhering to both HIPAA and any specific state-level regulations.
How to Ensure Your EMR is Truly Compliant
Vendor claims are a starting point, but your due diligence is what ensures protection. Here’s how we verify that a chosen HIPAA compliant EMR solution is robust:
- Scrutinizing the Business Associate Agreement (BAA): We carefully review every clause of the BAA from the EMR vendor. This document must clearly outline the vendor’s responsibilities, including implementing all required HIPAA safeguards, reporting any security incidents or breaches to you without delay, and specifying how your data will be returned or destroyed upon contract termination. A vendor’s refusal to sign a BAA or resistance to standard clauses is an immediate disqualification.
- Requesting Third-Party Audit Reports (SOC 2): A Service Organization Control 2 (SOC 2) report provides an independent auditor’s opinion on a vendor’s security controls. A SOC 2 Type I report assesses the design of controls at a single point in time, while a Type II report tests their operational effectiveness over a period (e.g., 6-12 months). We always request a Type II report, as it provides much stronger assurance of a vendor’s ongoing commitment to robust security.
- Verifying ONC Health IT Certification (CHPL): We check the Certified Health IT Product List (CHPL) to verify that the EMR solution has received ONC-ACB Certification. This certification indicates that the software meets specific functional and security requirements mandated by federal programs, including those in the 21st Century Cures Act. This act promotes patient data access through secure APIs and prohibits “information blocking,” making ONC certification a key indicator of a modern, interoperable, and compliant system.
- Asking Detailed Questions About Security Architecture: We directly inquire about the specific encryption standards used (e.g., AES-256 for data-at-rest, TLS 1.2+ for data-in-transit), data segregation methods in multi-tenant cloud environments, and disaster recovery procedures. A truly compliant vendor will be transparent and able to provide detailed answers.
Supporting Patient Rights and Engagement
A HIPAA compliant EMR is also a critical tool for empowering patients with control over their own health information, as mandated by the HIPAA Privacy Rule.
- Patient Access to Records: Patients have a right to view and obtain a copy of their health information. The EMR must facilitate this access in a timely and secure manner, often via the patient portal.
- Amendment Requests: If a patient identifies an error in their record, they have the right to request an amendment. The EMR must have a workflow to manage these requests, allowing providers to accept or deny them while maintaining a clear audit trail of the original information and the request itself.
- Accounting of Disclosures: Patients can request an accounting of certain disclosures of their ePHI made by the organization. The EMR’s audit trail functionality is essential for generating these reports, which must detail who received the information, when, and for what purpose (excluding routine uses like treatment, payment, and healthcare operations).
- Secure Messaging: Patients need a confidential way to communicate with their healthcare providers. The EMR’s secure messaging features enable these conversations, ensuring sensitive health information remains protected and part of the official medical record, unlike insecure channels like standard email or SMS.
Advanced Challenges and the Future of Compliant EMRs
The landscape of healthcare technology is constantly evolving, bringing both incredible opportunities and new compliance challenges. As we look to the future, our HIPAA compliant EMR strategies must adapt to phenomena like increasing interoperability, the rise of artificial intelligence (AI), and ongoing regulatory changes to remain effective.
Implementation and Interoperability Problems
Implementing and maintaining a HIPAA compliant EMR is a significant undertaking with several inherent challenges:
- Data Migration Risks: Moving patient data from legacy systems or a previous EMR is a high-stakes process. It is fraught with risks of data corruption, data loss, and security vulnerabilities during transfer. A detailed migration plan with validation checks is crucial for ensuring data integrity and security.
- Staff Training and Adoption: A new EMR system requires extensive training for all staff, representing a substantial investment in time and resources. Inadequate training is a primary cause of human error, which remains a leading factor in data breaches. Overcoming resistance to change and ensuring proficient use are key to realizing the EMR’s benefits.
- Complex System Integration: EMRs rarely exist in a vacuum. They must integrate with other systems like laboratory information systems (LIS), radiology information systems (RIS), and billing platforms. Each integration point, often managed via an Application Programming Interface (API), introduces a potential vulnerability. Securing these APIs and adhering to interoperability standards like FHIR (Fast Healthcare Interoperability Resources) is critical for maintaining end-to-end HIPAA compliance.
- Maintaining Compliance Across Connected Ecosystems: Interoperability complicates compliance exponentially. If an EMR connects with a third-party application (e.g., a patient-facing health app), it necessitates an additional Business Associate Agreement and thorough vetting of that application’s security. Ensuring ePHI remains protected as it moves between systems is a continuous and complex challenge for any healthcare organization.
- Cost and Scalability: The costs of HIPAA compliant EMR solutions vary significantly based on practice size, required features, and deployment model (cloud vs. on-premise). Smaller practices might find the financial burden of a comprehensive, certified EMR prohibitive, while larger organizations face challenges of scalability and integration across multiple departments and locations.
The Impact of AI on Your HIPAA Compliant EMR
Artificial Intelligence (AI) is rapidly changing healthcare, offering incredible potential for improved diagnostics, personalized treatment, and operational efficiency. However, integrating AI into HIPAA compliant EMR systems introduces a new and complex layer of risk for patient data security.
- AI for Clinical and Administrative Tasks: AI tools, including ambient listening technology, can automatically convert patient-provider conversations into structured clinical notes, saving providers hours of documentation time. They can also process unstructured data from faxes, generate referral letters, and optimize billing codes. These tools streamline workflows but require careful consideration of how the AI models handle, store, and secure the ePHI they process.
- Predictive Analytics and Clinical Decision Support: AI-powered predictive analytics can identify patients at high risk for certain conditions, flag potential care gaps, and support value-based care initiatives. These insights are invaluable but rely on analyzing vast datasets of ePHI, creating a large and attractive target for attackers.
- Novel Data Security Risks of AI Models: AI models introduce unique risks. For example, a malicious actor could launch a “membership inference attack” to determine if a specific individual’s data was used to train a model, or a “model inversion attack” to potentially reconstruct parts of the sensitive training data itself. Mitigating these risks may require advanced techniques like differential privacy or federated learning, where the model is trained on decentralized data without the data ever leaving its secure environment.
- Ensuring AI Vendors are True Business Associates: Just like any other vendor handling ePHI, any AI solution provider integrated with your HIPAA compliant EMR must sign a comprehensive Business Associate Agreement (BAA). This BAA must explicitly cover how ePHI is used for model training and inference, how data is protected, and who is liable in the event of an AI-related breach.
- Governance for AI-Generated Data and Insights: AI systems generate new data and insights that become part of the patient record. Clear governance frameworks are needed to manage this AI-generated data, ensuring its accuracy, integrity, and compliance with HIPAA. This includes addressing issues of algorithmic bias, creating processes to validate AI outputs before they influence clinical decisions, and maintaining auditable records of how and when AI was used in a patient’s care. Lifebit’s federated AI platform is designed to address these challenges, enabling secure analysis and model training across distributed datasets while maintaining strict governance and compliance with frameworks like HIPAA.
Preparing for Upcoming HIPAA Rule Changes
HIPAA is not a static rule; it evolves to address new technologies and emerging threats. We must stay ahead of the curve to maintain our HIPAA compliant EMR status.
- Proposed Security and Privacy Rule Updates: The HHS Office for Civil Rights has proposed significant updates to the HIPAA Privacy Rule (NPRM-2021) aimed at strengthening patient access rights and facilitating better care coordination. Concurrently, new Security Rule standards are anticipated to address modern cybersecurity threats.
- Mandatory Multi-Factor Authentication (MFA): While currently an “addressable” safeguard, future rules are widely expected to make multi-factor authentication (MFA) a mandatory requirement. MFA adds a critical layer of security beyond just a password, significantly reducing the risk of unauthorized access from stolen credentials.
- Solidifying Encryption Requirements: The proposed changes are also expected to formally mandate encryption for ePHI both at-rest and in-transit, moving this long-standing best practice to a strict, non-negotiable requirement.
- Alignment with HHS Cybersecurity Performance Goals (CPGs): The U.S. Department of Health and Human Services (HHS) has outlined voluntary Cybersecurity Performance Goals (CPGs) for the healthcare sector. These goals emphasize proactive measures like asset management, network segmentation, and robust incident response. Adopting a secure EMR that aligns with these CPGs now can help practices get ahead of impending regulatory changes and build a more resilient security posture.
Frequently Asked Questions about HIPAA Compliant EMRs
What is the role of a Business Associate Agreement (BAA) with an EMR vendor?
A Business Associate Agreement (BAA) is a legal contract between a healthcare provider (Covered Entity) and an EMR vendor (Business Associate) that handles Protected Health Information (PHI). Our BAA outlines the vendor’s responsibilities to safeguard PHI, comply with HIPAA rules, and report any breaches. Without a BAA, sharing PHI with a vendor is a HIPAA violation. The BAA is your assurance that the vendor is committed to protecting patient data.
Can a cloud-based EMR be HIPAA compliant?
Absolutely. A cloud-based EMR can be a HIPAA compliant EMR, provided the cloud service provider (CSP) and the EMR vendor implement the necessary safeguards and enter into a BAA. The cloud infrastructure must be HIPAA compliant, ensuring ePHI is encrypted, access is controlled, and audit trails are maintained. Leading cloud providers like AWS, Azure, and Google Cloud Platform offer HIPAA-compliant environments. When we choose a cloud-based EMR, we ensure the vendor demonstrates compliance and that a comprehensive BAA is signed.
How much do HIPAA-compliant EMR solutions typically cost?
The cost of HIPAA compliant EMR solutions varies based on practice size, required features, vendor, and deployment model (cloud vs. on-premise). Costs can range from a few hundred dollars per provider per month for basic services to tens of thousands in upfront costs and ongoing fees for extensive systems. These costs typically include licensing, implementation, training, and support. It’s crucial to conduct a thorough needs assessment and budget analysis, weighing the investment against the benefits of improved security, efficiency, and compliance.
Conclusion: Future-Proofing Your Practice with Secure Data Technology
Navigating HIPAA compliant EMR solutions is a complex but essential task in modern healthcare. We’ve covered the fundamental requirements, from the three pillars of HIPAA safeguards to the due diligence needed to verify vendor compliance through BAAs, SOC 2 reports, and ONC certifications.
The journey doesn’t end with implementation. Healthcare technology is a dynamic field, constantly evolving with new challenges like interoperability and the integration of AI. Preparing for upcoming HIPAA rule changes, such as mandatory MFA and improved encryption, is crucial for future-proofing our practices.
Achieving and maintaining a HIPAA compliant EMR system is about more than just avoiding penalties; it’s about building patient trust, enhancing operational efficiency, and securing the sensitive data at the core of healthcare. As the volume and complexity of biomedical data grow, the need for secure, compliant data analysis becomes even more pronounced.
At Lifebit, we understand these challenges intimately. Our next-generation federated AI platform is purpose-built to enable secure, real-time access to global biomedical and multi-omic data. With built-in capabilities for harmonization, advanced AI/ML analytics, and federated governance, we empower biopharma, governments, and public health agencies to conduct large-scale, compliant research. Our platform components, including the Trusted Research Environment (TRE) and Trusted Data Lakehouse (TDL), deliver real-time insights and secure collaboration, ensuring your data analysis is always compliant.
By prioritizing robust security measures and staying informed about the evolving regulatory landscape, we can ensure our HIPAA compliant EMR systems serve as powerful tools for better patient care, rather than potential liabilities.

