Mastering Data Access Control for Better Security

Why Data Access Control Is the Foundation of Modern Data Security
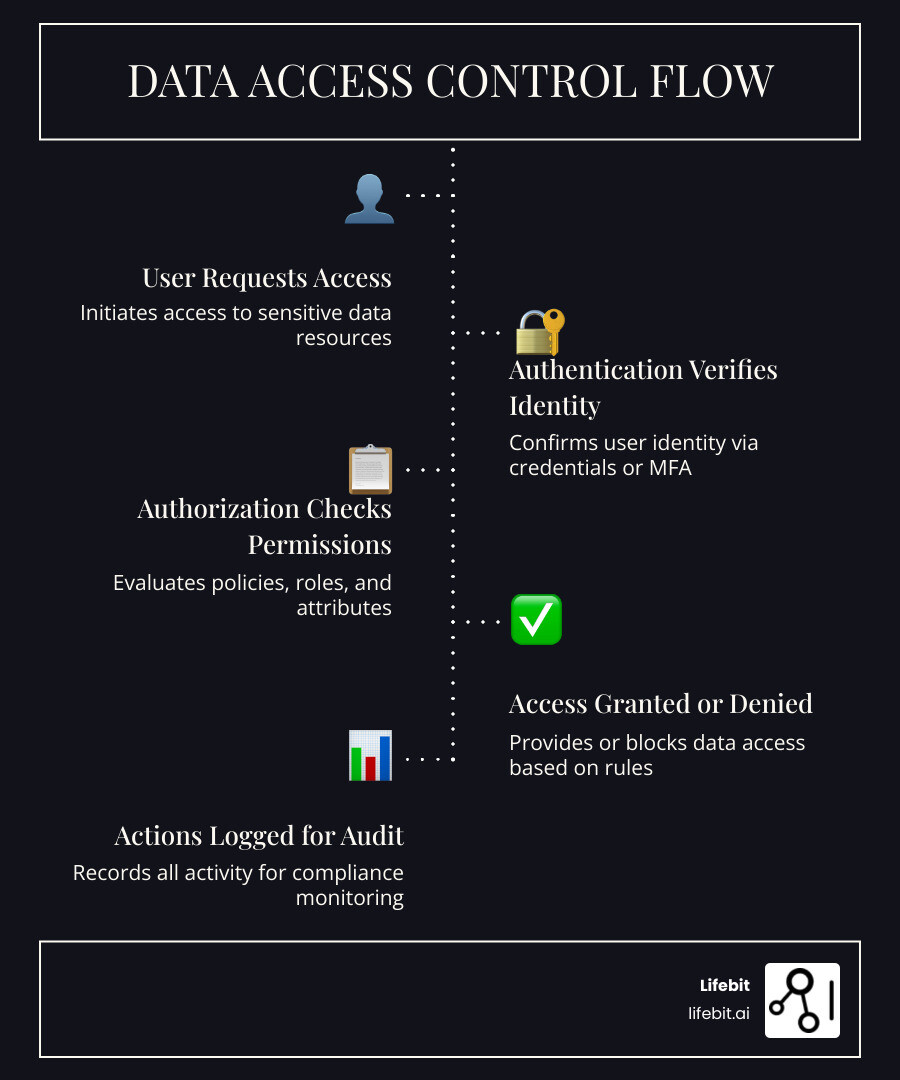
Data access control is the practice of restricting who can view, modify, or use specific data within your organization. It combines authentication (verifying identity) and authorization (granting permissions) to ensure sensitive information remains secure, compliant, and accessible only to those who need it.
Quick answer for decision-makers:
- What it does: Manages who accesses what data, when, and how
- Why it matters: Prevents breaches, ensures regulatory compliance, and maintains operational trust
- Core components: Authentication, authorization, policies, and continuous monitoring
- Key models: Role-Based (RBAC), Attribute-Based (ABAC), Mandatory (MAC), and Discretionary (DAC)
- Best practice: Apply the Principle of Least Privilege (PoLP) from day one
The stakes are high. One of the primary causes of data breaches is employees having access to data they shouldn’t—whether through misconfiguration, outdated permissions, or insider threats. Organizations face hefty fines under regulations like GDPR, HIPAA, and CPRA when access controls fail. Beyond financial penalties, breaches erode public trust and damage brand reputation in an era where data privacy has become a newsworthy topic.
Modern data environments are complex. Healthcare institutions safeguard millions of patient records. Pharmaceutical companies protect proprietary research spanning genomics, multi-omic datasets, and clinical trial results. Public sector agencies manage sensitive population health data across siloed systems. Without robust access control, these organizations cannot enable secure collaboration, real-time analytics, or federated research—all while meeting strict regulatory requirements.
I’m Maria Chatzou Dunford, CEO and Co-founder of Lifebit, where we’ve built a federated biomedical data platform enabling secure, compliant data access control across 275+ million patient records for global pharma, public sector, and regulatory organizations. Over 15 years working in computational biology, genomics, and health-tech, I’ve seen how proper data access control unlocks innovation while protecting what matters most.
Data access control terms made easy:
- biomedical data access
- I’m looking for services that provide access to anonymized patient data for research purposes.
- health data ecosystem
What is Data Access Control and Why Your Organization is at Risk
At its heart, data access control refers to the tools, methodologies, and policies you implement to control who is granted access to what data. As your business grows and more people work with your data, it is easy to make mistakes that can lead to damaging data leaks. Without a clear framework, you are essentially leaving the keys to your most valuable assets in the front door lock.
Data breaches have become a newsworthy topic. The public is increasingly aware of the value and sensitivity of their personal information—and its usefulness to bad actors looking to extort, imitate, or harass. For organizations, the risk isn’t just a “tech problem”; it’s a fundamental threat to Data Privacy Research and organizational longevity.

The High Cost of Unauthorized Access
Unauthorized access occurs when someone views or uses data without the proper permissions. This could be an external hacker using stolen credentials, or an internal developer using application credentials to access a table they shouldn’t see. The consequences are often measured in millions of dollars.
Companies are regularly fined for infractions of privacy regulations. Whether it’s Personally Identifiable Information (PII) or Protected Health Information (PHI), the legal hammer is heavy. Under the GDPR, fines for inadequate data protection measures can reach up to 4% of annual global turnover. In the US, HIPAA violations can lead to massive settlements that cripple smaller healthcare providers.
Maintaining Operational Efficiency and Trust
It’s not all about avoiding fines, though. Effective data access control is about preserving the integrity of your data. When only authorized users can modify records, you ensure data accuracy and reliability.
Furthermore, “democratization” of data analytics tools means more employees than ever are poking around in datasets. If they aren’t guided by strict access controls, they might accidentally delete a critical table or misinterpret sensitive results. A strong security posture builds user confidence and protects your brand reputation, showing customers that you take their privacy seriously.
How Data Access Control Works: Authentication vs. Authorization
To master data access control, you must understand the two pillars it stands on: Authentication and Authorization. Think of it like a high-security lab: Authentication is the ID badge that proves you are who you say you are. Authorization is the clearance level that determines which rooms you can actually enter.
| Feature | Authentication (Identity) | Authorization (Permissions) |
|---|---|---|
| Purpose | Verifies the user’s identity. | Determines what the user can do. |
| Methods | Passwords, Biometrics, MFA. | RBAC, ABAC, ACLs. |
| Example | Logging in with a username and password. | Being allowed to “Read” but not “Edit” a file. |
We often use AI Enabled Data Governance to help automate these checks, ensuring that even as thousands of requests come in, they are all handled according to the rules.
The Mechanics of Modern Data Access Control
Modern systems go beyond a simple “yes/no” to access. We use sophisticated Access control measures like multi-factor authentication (MFA) to ensure that a stolen password isn’t enough for a breach.
Once identity is verified, we must Secure data at rest and in transit. This involves:
- Data Masking: Scrambling sensitive fields (like Social Security numbers) so that even if an analyst sees the record, they can’t see the sensitive parts.
- Encryption: Making the data unreadable to anyone without the decryption key.
- Granular Permissions: Giving a user access to a specific row or column rather than the entire database.
Centralizing Identity with LDAP and Active Directory
In an enterprise, you can’t manage users one by one. You need a “source of truth.” This is where LDAP and Active Directory come in. These tools centralize user management, allowing you to onboard or offboard employees across all your systems at once.
Using protocols like SCIM (System for Cross-domain Identity Management), we can automate user provisioning. When a new bioinformatician joins your team, SCIM automatically creates their accounts in your data platforms and assigns the right roles based on their department.
5 Essential Models for Managing Data Access
Choosing the right model is critical for scalability. You don’t want your data engineering team to become a bottleneck, manually approving every single access request.
- Discretionary access control (DAC): The owner of the data decides who gets access. It’s flexible but risky for large organizations because it relies on individual users making good security decisions.
- Mandatory access control (MAC): A central authority assigns “clearance levels” to users and “classifications” to data. If your level doesn’t match the data’s classification, you’re out. This is the gold standard for military and government security.
- Role-based access control (RBAC): Access is based on job function. If you are in the “Genomics Research” group, you get the permissions assigned to that group. It’s the most common model for businesses.
- Data-Centric Control: Focuses on the sensitivity of the data itself, regardless of who is asking.
- Context-Centric Control: Looks at the “how” and “where”—for example, denying access if a user tries to log in from an unknown IP address at 3 AM.
To learn more about how these fit into a broader strategy, check out our Secure Data Environment Complete Guide.
Scaling with Attribute-Based Data Access Control (ABAC)
As organizations grow, RBAC can lead to “role explosion” (having 5,000 different roles for 5,000 employees). This is where Attribute-based access control shines.
ABAC uses dynamic rules. Instead of saying “John has the Researcher role,” ABAC says “Access is granted if the user is a Researcher AND the project is ‘Cancer Study’ AND they are using a company laptop.” This fine-grained control is detailed in the NIST Guide to Attribute Based Access Control (ABAC), which we highly recommend for enterprise architects.
Policy-Based Access Control (PBAC) for Cloud Environments
For cloud-native ecosystems, PBAC takes ABAC a step further by using a centralized access control policy that can be applied across different apps and databases. It allows for massive scalability because you can update one policy and have it instantly enforced across your entire global infrastructure.
Implementing the Principle of Least Privilege (PoLP)
If there is one rule to live by in data access control, it is the principle of least privilege. This means giving users only the absolute minimum access they need to do their jobs—and nothing more.
This prevents the bystander effect in security, where everyone assumes “someone else” is watching the data. By strictly limiting who can see what, you ensure accountability. This is a core requirement of most Data Privacy Regulations.
Reducing the Attack Surface
The “attack surface” is the sum of all points where an attacker could try to enter or extract data. By using least-privileged access controls, you shrink that surface.
- Default Deny: Start by giving everyone zero access.
- Just-in-Time Access: Grant permissions only for the duration of a specific task.
- Minimal Permissions: If someone only needs to read a report, don’t give them edit rights to the underlying database.
Auditing and Continuous Monitoring
You can’t just set it and forget it. You need Security information and event management (SIEM) tools to track every access attempt. If an account that usually only accesses 10 records a day suddenly tries to download 10,000, your system should flag it as an anomaly.
In a Federated Data Governance model, this monitoring happens across all your different data sites, providing a single view of who is doing what, regardless of where the data actually lives.
Overcoming Enterprise Challenges and Regulatory Hurdles
Scaling data access control across a global organization is hard. You’re dealing with a “compliance alphabet soup” including HIPAA in the US, CPRA in California, and LGPD in Brazil.
One critical step is ensuring you have data processing agreements (DPAs) with any third-party vendors. These legal documents stipulate exactly how they are allowed to handle your data and what access controls they must have in place.
Solving the Data Silo Problem
The biggest challenge posed by data access management is often the data silo. When data is scattered across different departments, each with its own rules, security becomes impossible to manage.
Centralized governance is the answer. By using a Data Governance Platform Complete Guide, you can create a unified set of access rules that apply to all your data, whether it’s in a cloud warehouse or an on-premise server. This interoperability ensures that your security doesn’t break when data moves between systems.
Training Employees to Prevent Social Engineering
Technology can only do so much. A huge portion of breaches start with a phishing email. Employee training is essential. Your team needs to understand:
- Password Hygiene: Using strong, unique passwords and MFA.
- Incident Response: Who to call the second they think they’ve made a mistake.
- Social Engineering: How to spot a “Dementor of Data Engineering” trying to trick them into giving up their credentials.
Frequently Asked Questions about Data Access Control
What is the difference between authorized and unauthorized access?
Authorized access follows established policies for legitimate users—like a doctor viewing their own patient’s chart. Unauthorized access involves compromised credentials, misconfigurations, or insider threats—like a developer using their database “admin” rights to look at payroll data they aren’t supposed to see.
How does data access control integrate with GDPR and HIPAA?
It is the technical backbone of these regulations. It ensures that sensitive personal and health data is only accessible to “need-to-know” personnel. By maintaining strict logs, it provides the audit trails required to prove compliance during a regulatory inspection.
Why is the Principle of Least Privilege (PoLP) so important?
PoLP is your best defense against “lateral movement.” If a hacker steals the password of a junior marketing assistant, PoLP ensures they only get access to marketing files—not the company’s financial records or proprietary research. It minimizes the blast radius of any security incident.
Conclusion
Mastering data access control isn’t just about locking doors; it’s about building a foundation for innovation. When you know your data is secure, you can collaborate more freely, analyze more deeply, and scale more rapidly.
At Lifebit, we specialize in making this complex process simple. Our Lifebit Federated Biomedical Data Platform is designed to provide granular, policy-driven access to the world’s most sensitive data. We help you move past the “all or nothing” approach to security, enabling a world where data can be used to its full potential without ever compromising on privacy.
Ready to secure your data while empowering your researchers? Let’s talk about how federated governance can transform your organization.

