Healthcare Data Privacy Compliance and the Prescription for Success

Why Healthcare Data Privacy Compliance Matters More Than Ever
Healthcare data privacy compliance is the set of laws, regulations, and practices that protect sensitive patient information from unauthorized access, use, or disclosure while enabling effective healthcare delivery. In Ontario alone, the Personal Health Information Protection Act (PHIPA) safeguards over 15 million patient records, while globally, regulations like HIPAA in the United States and GDPR in the European Union create a complex web of requirements that healthcare organizations must steer.
Key regulations governing healthcare data privacy compliance:
- PHIPA (Ontario) – Protects personal health information for 15M+ residents; requires consent for collection, use, and disclosure; grants access and correction rights
- HIPAA (United States) – Establishes national standards for protected health information; applies to health plans, clearinghouses, and providers; penalties up to $1.5M annually
- GDPR (European Union) – Treats health data as “special category” requiring extra protection; mandates 72-hour breach notification; fines up to 4% of global revenue
- FIPPA (Ontario public sector) – Governs freedom of information and privacy for government health entities like Ontario Health
- Breach notification requirements – PHIPA requires immediate notification to affected individuals and the Information and Privacy Commissioner; HIPAA allows 60 days; GDPR requires 72 hours
Healthcare organizations face penalties ranging from $100 to $63,973 per violation under HIPAA, while GDPR fines can reach €20 million or 4% of annual global turnover. In Ontario, the Information and Privacy Commissioner enforces PHIPA through Administrative Monetary Penalties (AMPs), independent reviews, and public enforcement actions.
As CEO and Co-founder of Lifebit, I’ve spent over 15 years working at the intersection of genomics, AI, and secure data platforms, helping public sector institutions and pharmaceutical organizations steer healthcare data privacy compliance across federated, multi-jurisdictional environments. My team and I have built systems that enable analysis of sensitive biomedical data without compromising patient privacy or regulatory requirements.
Master PHIPA: How Ontario’s Privacy Laws Protect 15M+ Patients
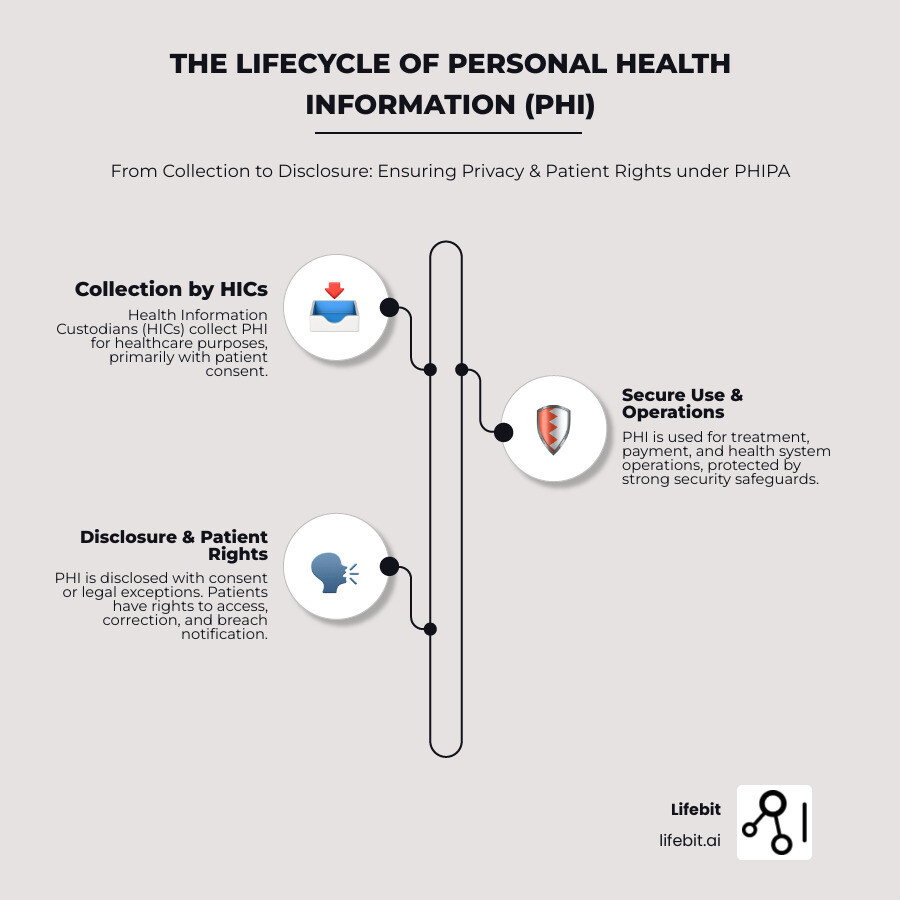
In Ontario, the cornerstone of health privacy is the Personal Health Information Protection Act, 2004 (PHIPA). This legislation was designed to balance two critical needs: protecting the confidentiality of individuals’ health information and facilitating the effective delivery of healthcare. While PHIPA is the primary law, it often works alongside the Freedom of Information and Protection of Privacy Act (FIPPA) and the Gift of Life Act, particularly when dealing with public sector organizations like Ontario Health.
Ontario Health is a prime example of an organization that must steer these layers. As a “Prescribed Organization” under PHIPA, it requires access to data from across the province to fulfill its mandate. However, this access comes with strict obligations. They must maintain Healthcare Data Compliance by making specific information public, such as data asset lists and privacy impact assessment summaries.
The law applies to Health Information Custodians (HICs). These are the “gatekeepers” of your data. The list of HICs includes:
- Health care practitioners (doctors, nurses, etc.)
- Public and private hospitals
- Pharmacies and medical laboratories
- Long-term care homes and retirement homes
- The Ministry of Health
The “Circle of Care” and Implied Consent
One of the most unique aspects of PHIPA is the concept of the “Circle of Care.” This is not a legal term found in the act itself, but a shorthand used to describe the conditions under which a HIC may rely on a patient’s implied consent to share their personal health information with other providers for the purpose of providing care. For the Circle of Care to apply, the HIC must be providing healthcare to the individual, the information must be shared for that purpose, and the HIC must not have been informed that the individual has expressly withheld or withdrawn consent. This allows for the seamless flow of information between a family doctor, a specialist, and a hospital pharmacist without requiring a signed form at every step.
The “Lockbox” Provision
Patients in Ontario have the right to “lock” their records. This means they can instruct a HIC not to disclose specific parts of their health information to other providers, even within the circle of care. While this empowers patients, it also creates technical challenges for HICs, who must ensure their electronic systems can flag and respect these “lockbox” instructions while still ensuring that life-saving information is available in emergencies.
Health Information Network Providers (HINPs)
As healthcare becomes more digitized, the role of Health Information Network Providers (HINPs) has become critical. A HINP is an entity that provides services to two or more HICs to enable them to share PHI electronically. Under PHIPA, HINPs have their own set of obligations, including the requirement to perform privacy impact assessments and to notify HICs of any unauthorized access or breaches. This ensures that the infrastructure providers are held to the same high standards as the doctors and hospitals they serve.
Research published in Scientific research on global healthcare data privacy highlights that these regional disparities in definitions can make global research difficult, but in Ontario, the HIC and HINP models provide a clear chain of accountability.
How PHIPA and FIPPA Interact
Navigating the public sector requires understanding how PHIPA interacts with FIPPA. Generally, PHIPA is a “stand-alone” health privacy law. This means that if there is a conflict between PHIPA and FIPPA regarding personal health information, PHIPA usually takes precedence.
FIPPA governs the right of access to information held by public institutions and the protection of personal information (PI) that isn’t necessarily health-related. However, when public entities act as “Data Integration Units,” they may handle both PI and PHI. At Lifebit, we emphasize that a Data Governance Platform Complete Guide must account for these legislative overlaps to ensure that “freedom of information” does not accidentally lead to a privacy breach.
Avoid $1M Penalties: The Rules of Healthcare Data Privacy Compliance
The Information and Privacy Commissioner of Ontario (IPC) is the watchdog with the power to bite. The IPC oversees compliance and has the authority to conduct reviews, resolve complaints, and issue Administrative Monetary Penalties (AMPs).
The 2024 AMPs Framework
As of 2024, the IPC has expanded powers to issue Administrative Monetary Penalties (AMPs) for contraventions of PHIPA. These penalties are designed to be punitive and deterrent, rather than just compensatory. For individuals, fines can reach up to $50,000, while for corporations and organizations, they can soar to $500,000 per violation. These penalties can be issued without the need for a court order, making the IPC’s enforcement actions much swifter than in previous years. This shift signals a move toward a “zero-tolerance” policy for systemic negligence in Data Integrity in Health Information Systems.
Securing the Digital Frontier: Healthcare Data Privacy Compliance in EHRs
As we move toward a fully digital health system, Electronic Health Records (EHRs) and digital health identifiers present new risks. PHIPA includes specific provisions for these technologies. Custodians using electronic systems are required to maintain electronic audit logs. These logs must record:
- The identity of the person who accessed the PHI
- The date and time of the access
- The specific record or component of the record that was viewed
- Any modifications or deletions made to the data
These logs must be kept for a minimum period (often several years) and must be available for review by the IPC. The Minister of Health can also issue directives regarding the protection of EHRs. We believe that Preserving Patient Data Privacy and Security in these digital environments requires more than just a password; it requires a culture of security where every digital “footprint” is tracked and justified.
Mandatory Breach Notification and IPC Enforcement
One of the most critical obligations under PHIPA is the mandatory breach notification. If PHI is stolen, lost, or accessed by an unauthorized person, the custodian must:
- Notify the affected individual at the first reasonable opportunity. This notice must include a description of the breach and the steps the individual can take to protect themselves.
- Notify the IPC in specific circumstances, such as when the breach involves a large number of individuals, when there is a risk of significant harm, or in cases of “snooping” by employees.
“Snooping”—the unauthorized viewing of health records by staff out of curiosity or malice—is one of the most common causes of IPC investigations. The IPC has the power to investigate these incidents and issue orders to change organizational practices, including mandatory staff retraining and the implementation of automated monitoring tools. Using AI for Regulatory Compliance is becoming a standard way for large organizations to detect these anomalies in real-time before they escalate into a crisis.
Global Standards: Why HIPAA and GDPR Aren’t Enough
While we focus on Ontario, many of our partners operate globally. It is a mistake to assume that being HIPAA compliant automatically makes you PHIPA compliant. Each jurisdiction has its own nuances regarding data residency, consent models, and the definition of “de-identified” data.
The Challenge of Data Sovereignty
Data sovereignty refers to the concept that data is subject to the laws of the country in which it is located. For healthcare organizations using cloud services, this is a major compliance hurdle. For example, if an Ontario hospital stores PHI on a server located in the United States, that data may be subject to the US Patriot Act, which could conflict with PHIPA’s privacy protections. This is why many Canadian organizations insist on “data residency” within Canada, ensuring that sensitive health data never crosses the border.
De-identification vs. Anonymization
A major point of divergence between GDPR and PHIPA is the standard for de-identification. Under GDPR, data is only considered “anonymous” if the process is irreversible. If there is any technical possibility of re-identification, the data is still considered “pseudonymous” and remains subject to the full weight of the regulation. PHIPA, however, uses a “reasonableness” standard. Data is considered de-identified if it is no longer reasonable to believe that the information could be used, alone or in combination with other information, to identify an individual. This subtle difference has massive implications for how researchers can use secondary data.
- GDPR (Europe): Focuses on “data minimization” and treats health data as a “special category” requiring explicit consent. It sets a global benchmark for 72-hour notifications and includes the “Right to be Forgotten.”
- HIPAA (USA): Primarily concerns “covered entities” and “business associates,” focusing heavily on encryption and access for ePHI. It lacks the broad “individual rights” found in PHIPA or GDPR.
- POPIA (South Africa): Similar to GDPR, it emphasizes the lawful processing of personal information and requires a designated Information Officer for every entity.
Research in Scientific research on blockchain and AI in healthcare suggests that emerging technologies like blockchain can help bridge these jurisdictional gaps by providing immutable ledgers. For those of us handling GDPR Compliant Data, we know the “Right to be Forgotten” is a unique challenge that PHIPA doesn’t mirror exactly, as health records in Ontario have strict retention requirements.
| Feature | PHIPA (Ontario) | HIPAA (USA) | GDPR (EU) |
|---|---|---|---|
| Primary Focus | Health Information Custodians | Covered Entities | All Data Controllers |
| Consent | Implied (Circle of Care) or Express | Required for non-TPO uses | Explicit for Special Categories |
| Breach Notification | Immediate (to individual) | Within 60 days | Within 72 hours |
| Penalties | AMPs and Civil Damages | Up to $1.9M/year (adjusted) | Up to 4% of Global Turnover |
Future-Proofing Healthcare Data Privacy Compliance with AI
The “holy grail” of healthcare data privacy compliance is the use of de-identified data for research. However, the risk of “re-identification” is real. Advanced AI can sometimes “guess” an identity by cross-referencing de-identified health data with public datasets like voter registries or social media. This is where Privacy Preserving AI comes in. By using federated learning, we can train models on data without the data ever leaving its original, secure location. This allows for secondary use of data for research while keeping the re-identification risk at near-zero.
5 Steps to Bulletproof Your Health Information Practices
Compliance is not a one-time event; it is a continuous process. We recommend a five-step approach to ensure your organization meets the highest standards of healthcare data privacy compliance.
Step 1: Establish Knowledgeable Consent
Consent is the foundation of PHIPA. It must be knowledgeable, meaning the individual must understand why their information is being collected and that they have the right to withhold or withdraw consent.
- Implied Consent: Often used within the “circle of care” (e.g., a GP sharing info with a specialist for treatment). This relies on the “Notice of Purposes” posted in the clinic or hospital.
- Express Consent: Required when disclosing PHI to a non-custodian (like an insurance company), for purposes other than healthcare (like marketing), or when disclosing PHI across provincial borders.
At Lifebit, we see Clinical Data Governance as the mechanism that manages these consent strings across complex data ecosystems, ensuring that a patient’s “no” is respected across all integrated systems.
Step 2: Empower Individual Rights
Under PHIPA, patients have the right to:
- Access: View and receive a copy of their PHI. Custodians must respond within 30 days, though extensions are possible in complex cases.
- Correction: Request that inaccurate or incomplete records be amended. If the HIC refuses, the patient has the right to attach a “Statement of Disagreement” to their file.
- Complaints: File a complaint with the IPC if they believe their rights have been violated.
Ensuring Secure Clinical Data access for patients while maintaining strict internal controls is a delicate but necessary balance. Organizations should implement secure patient portals that use multi-factor authentication (MFA) to verify identity.
Step 3: Implement Robust Security Safeguards
Custodians must take “reasonable steps” to protect PHI. This includes a three-pronged approach:
- Administrative Safeguards: These are the “people and processes” side of security. It includes comprehensive privacy policies, mandatory annual staff training, and signed confidentiality agreements for all employees and contractors.
- Technical Safeguards: These are the digital tools used to protect data. Key requirements include end-to-end encryption for data at rest and in transit, robust firewalls, and the use of unique user IDs and complex passwords.
- Physical Safeguards: These protect the hardware and paper records. Examples include locked filing cabinets, secure server rooms with restricted badge access, and “clean-desk” policies to ensure PHI isn’t left visible on desks or printers.
Our Lifebit ISO Certification: Genomic Data Security demonstrates that even the most sensitive data—DNA—can be handled with technical and administrative rigor that exceeds standard requirements.
Step 4: Privacy by Design (PbD)
Privacy by Design is a framework developed by former Ontario Privacy Commissioner Dr. Ann Cavoukian. It suggests that privacy should be the default setting for any system. This means:
- Proactive, not Reactive: Anticipating privacy risks before they happen.
- Privacy as the Default: Users shouldn’t have to change settings to protect their data.
- Full Functionality: You don’t have to sacrifice security for usability; it’s a “win-win” approach.
Understanding these legal nuances is a vital part of Data Privacy Research, especially in pediatric or geriatric care where substitute decision-makers are frequently involved.
Step 5: Conduct Privacy Impact Assessments (PIAs)
A PIA is a formal risk assessment of any new technology, program, or system that handles PHI. It is a structured process to identify and mitigate privacy risks. A thorough PIA should examine:
- What PHI is being collected and why?
- How is the data flowing through the system?
- What are the potential threats (e.g., hacking, accidental loss)?
- What safeguards are in place to mitigate those threats?
For a deep dive into how to automate this, see our AI-enabled Data Governance Ultimate Guide. A PIA should be a living document, updated whenever the system changes or new threats emerge. A comprehensive Secure Data Environment Complete Guide is essential for any organization looking to implement these steps effectively.
Frequently Asked Questions about PHIPA
What is a Health Information Custodian?
A Health Information Custodian (HIC) is an individual or organization described in PHIPA that has custody or control of personal health information in connection with their powers or duties. This includes doctors, hospitals, pharmacies, and the Ministry of Health.
How do I request access to my health records?
You can make a request directly to the health information custodian (e.g., your doctor or the hospital). They generally have 30 days to respond. While they can charge a “reasonable fee” for copies, they cannot deny access based on your inability to pay.
What are the penalties for a PHIPA violation?
Penalties can include Administrative Monetary Penalties (AMPs) issued by the IPC, as well as potential criminal prosecution for “willful” violations. Furthermore, individuals can seek damages in court for actual harm or mental anguish resulting from a breach.
Conclusion
Navigating healthcare data privacy compliance in a world of “big data” and AI requires more than just a legal checklist. It requires technology that is “secure by design.”
At Lifebit, we provide a next-generation federated AI platform that solves the fundamental tension between data access and data privacy. Our Trusted Research Environment (TRE) allows researchers to run advanced AI/ML analytics on global biomedical and multi-omic data without the sensitive information ever leaving the custodian’s secure infrastructure.
By implementing federated governance and real-time evidence layers (R.E.A.L.), we empower biopharma and public health agencies to collaborate securely across five continents. Whether you are in London, New York, Singapore, or Toronto, we ensure your research is compliant, scalable, and—most importantly—trusted.
For more information on how we safeguard the world’s most sensitive data, visit the More info about Lifebit Trust Center.

